This article is more than 1 year old
Robbing a bank? Carberp toolkit now available for just $5k
Trojan forum sale may mark split in Carberp gang
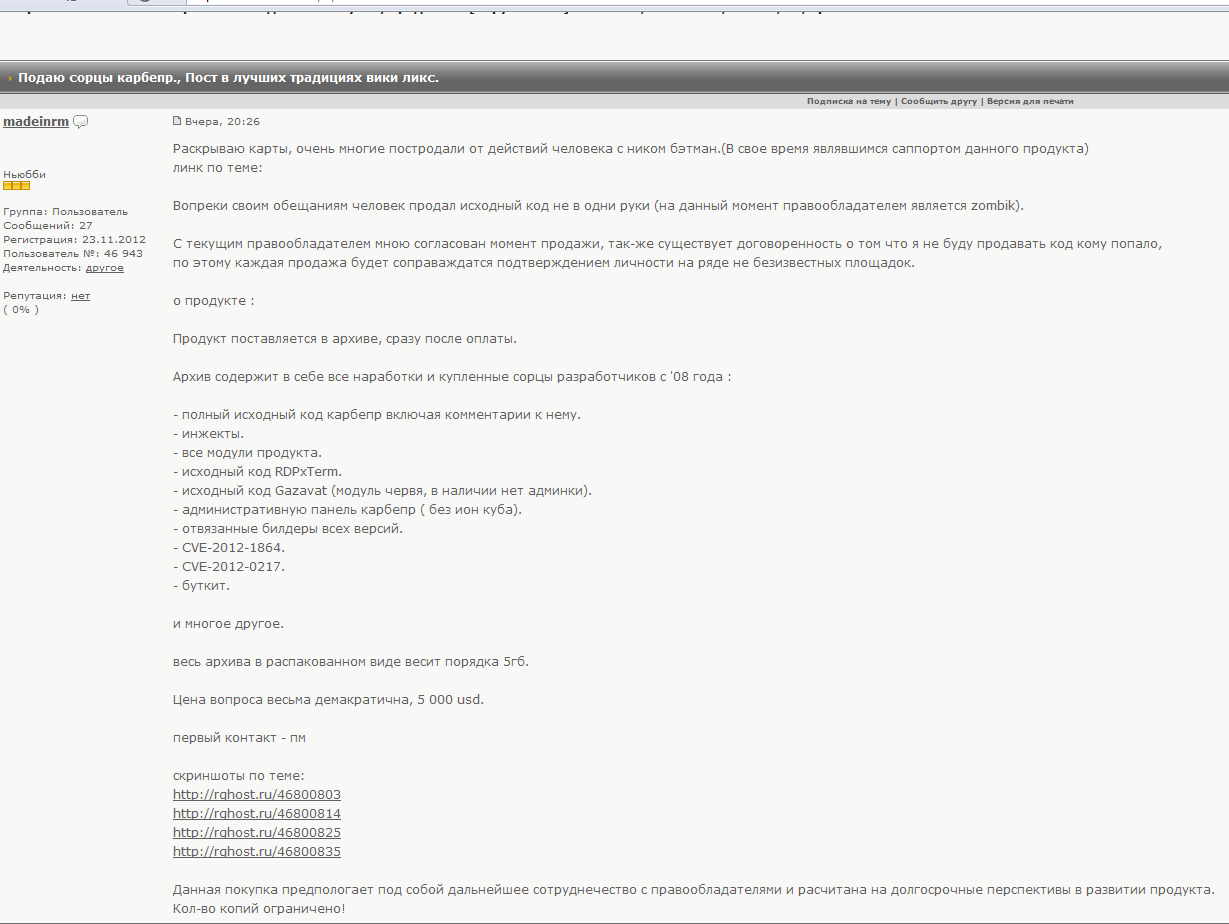
Cybercrooks are selling the source code for the Carberp banking Trojan toolkit through underground forums - at just $5,000 a pop.
The sale of the building blocks for the banking Trojan toolkit is a sign of "conflict within the team", according to Andrey Komarov of Russian security firm Group-IB.
"Some of the members would love to destroy the project and move onto another business or new product," Komarov told El Reg.
The toolkit for sale consists of the full source code of Carberp, including: comments; web-injects; all the Carberp modules; source code of Gazavar (the worm module); the admin panel for the command and control servers; Windows exploits related to vulnerabilities patched last year (specifically CVE-2012-1864 and CVE-2012-0217); a bootkit module, and many other components. The complete archive weighs in at 5GB.
Forum user "madeinrm" states that he is offering the source code for sale because someone else using the nickname "batman" had already passed on the source code to a third party, apparently against madeinrm's approval.
Madeinrm said he intends to screen potential customers but is nonetheless looking to sell the hitherto secret code powering the malware to a large number of people, rather than selling it at a higher price through an exclusive deal.
Carberp first emerged on the banking fraud scene around three years ago as a competitor to the dominant financial malware platforms Zeus and SpyEye. Russian police have made a number of arrests involving cybercriminals who used the malware to carry out electronic banking fraud.
Despite this, the core of the group actually developing the malware has remained intact and are continuing with their work, even sub-contracting out aspects of the creation of the code.
"Previously, Group-IB took part in the arrest of some members of Carberp group, which is an international group," Komarov explained. “For example, this team hired Chinese hackers for bootkit module developing, before starting the Carberp 2 project."
Group-IB reckons that there are currently around 12 active members within the Carberp gang, with most of them either from the Ukraine or Russia. Some members are thought to live in the European Union.
Komarov compared the circumstances surrounding the release of the Carberp source code with those around the release of the source code for ZeuS two years ago.
"This is very similar to how Zeus was leaked,” he said. “Someone tried to sell its source code too, but then the code was published on one of the filesharing networks hosting for free."
History appears to be repeating itself. Misunderstandings and conflict within the Zeus team are repeating themselves within the Carberp group. The most likely outcome of the rift with the Carberp group is a split, with elements going off to work on other malware-based projects, which might include even more powerful banking Trojan malware.
"We will probably receive something new instead of Carberp in the very near future," Komarov concluded. ®