This article is more than 1 year old
Mysterious 'Vladuz' again hacks eBay employee servers
He's ba-ack
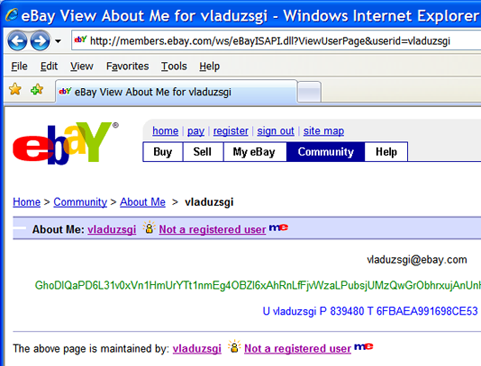
A hacker has once again managed to pilfer eBay credentials that allow him to masquerade as an official company representative even as he taunts eBay officials on the company's message boards. It's at least the second time the person going by the name Vladuz has pulled off the prank, which is causing many users to question the adequacy of eBay security.
The hacker, said to be living in Romania, claims to have acquired the ability to penetrate the company's perimeter at will. Combined with a rash of hacked accounts, the assertion has created a small but vocal group of users who believe eBay is covering up a massive back door in its defenses.
"Ugh, eBay is so rude *haha*" the intruder said in one post, left late on Thursday, California time.
eBay officials strenuously deny there is any such back door. They admit Vladuz was able to pilfer a limited number of credentials needed to pose as a customer service representative, but insist the servers that administer those functions are balkanized from databases where sensitive information such as customer records are kept. A spokesman said he was unsure if the hacker has access to the company's intranet, but said even if he does, he wouldn't be able to acquire much more than employee phone numbers and employee news. Just two days ago, eBay officials said they had quashed Vladuz's access to employee parts of the network, a claim the spokesman says now appears to be incorrect.
Like all good conspiracy theories, eBay's denials of anything more than a limited security breach has only fueled suspicions that something much more nefarious was afoot. "Nothing is compromised at eBay!" one forum participant, with just a bit of sarcasm, wrote shortly after Vladuz made his most recent appearance.
Even Vladuz couldn't resist registering his skepticism about a cover up. After quoting statements eBay spokesman Hani Durzy recently made to the effect that the hacker had only limited access, the intruder retorted: "Oh really? Crappy email servers, they seem to be linked to the main ebay servers, including financial servers. *haha* Durzy is a big liar." (screenshot here.)
According to Katherine Carington Smith, who is affiliated with the eBay-related blog Pheebay.com, this is the third time Vladuz has been able to enter eBay forums and make "pink postings," a reference to the color of borders designating comments from eBay officials.
Durzy says eBay officials have been working with the US Secret Service and law enforcement officials in Romania to close in on Vladuz. "We're still working with law enforcement to try to bring this guy to justice," he said.
eBay officials quickly removed the postings, but not before we took screen shots. Shortly after the posting of this article, Vladuz graced the German pages of an eBay forum. eBaymotorssucks.com has those screenshots here. ®
