This article is more than 1 year old
Attention Symantec: There's a bug crawling on your website
XSS strikes again
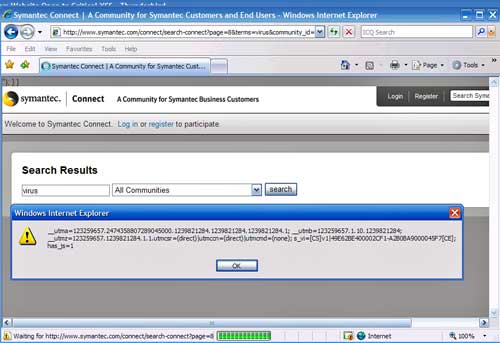
Symantec has been outed for hosting gaping security holes on its website that could allow miscreants to remotely execute malicious code on the computers of people who visit it.
The XSS, or cross-site scripting, bugs allow attackers to steal the web cookies Symantec sets on visitors' hard drives. Such cookies are frequently used to prove a visitor has already entered a valid password, so the ability to lift the file could be a non-trivial lapse of Symantec's security.
Other exploits showed it was possible to inject images from third-party websites such as imageshack.us. They were documented by a hacking collective that calls itself t3am3lite. Less-charitable hackers could exploit the hole to inject javascript or other types of code that exploits unpatched vulnerabilities or carries out other malicious acts.
It's the latest example of a large company or organization that should know better succumbing to garden-variety web bugs that put their users at risk. Along with SQL injections and CSRFs, or cross-site request forgeries, XSS attacks leave end-users open to malware and phishing attacks while visiting trusted websites.
Other sites that have suffered from them include anti-virus providers Kaspersky and BitDefender, financial services American Express and PayPal (repeatedly), and large government agencies including the Department of Homeland Security.
This cookie brought to you by XSS
The bugs can jeopardize a site's good standing with the PCI, or payment card industry, or possibly other regulatory frameworks.
Symantec officials have been notified of the bugs and are working to eradicate them, but at time of publication, the holes were still wide open. You can see more screen shots here. ®
