This article is more than 1 year old
Adobe plagued by 16-month-old XSS bug
Not to mention banks and ecommerce sites
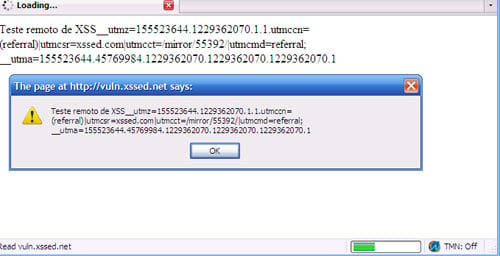
More than 16 months after researchers warned that critical vulnerabilities in Adobe Flash files leave websites vulnerable to phishing and other serious attacks, a wide array of pages - some hosted on Adobe.com itself - remain vulnerable.
The problem stems from buggy SWF files that generate banner ads and other animated content. In December 2007, a team of researchers discovered the files could be exploited by attackers to tamper with websites belonging to banks, government agencies and other trusted organizations. Over the next few months, the researchers repeatedly warned webmasters the problem would be difficult to fix, because it would require potentially millions of graphics files to be regenerated, often from scratch.
Those warnings now appear to be prescient. As the website XSSed has documented, even Adobe.com has failed to contain the offending SWF files. Other offenders include the Marfin Egnatia Bank and Greek electronics vendor Plaiso.gr. At time of writing, more than 24 hours after the XSSed item was published, all three sites remained vulnerable.
"Anyone who includes one of those ads in their site is now susceptible to cross-site scripting and some other things," said Jeff Williams, CEO of web application security firm Aspect Security who reviewed the posting. "It's definitely not good."
One reason the vulnerability has been so difficult to fix is that it requires multiple steps. First, web masters must patch the application they used to render the SWF files. Then they must examine every file hosted on their website and regenerate each one found to be buggy. The flaw resides inside the file's clickTAG= parameter, which can easily be manipulated to execute malicious scripts in the browsers of those who view the vulnerable content.
This XSS brought to you by Adobe
At the very least, sites that host the vulnerable files open themselves up to phishing attacks. In some cases, the vulnerability can be used to steal cookie files used to log a user in to sensitive parts of a website. ®
