This article is more than 1 year old
PerlMonks suffers unholy hack
Tidings without comfort or joy
Web developer site PerlMonks is obliging users to change up their passwords, following a successful hacking attack.
The community website, which provides a forum for users interested in Perl programming and related subjects, such as web applications and system administration, posted a notice (extract below) admitting the hacker had breached its systems in May. The breach - which exposed unencrypted passwords, together with associated names and email addresses, only came to light last week after hackers posted the passwords of high ranking users via an online magazine.
Some time on May 20, 2009, an unused (but still online) PerlMonks server was hacked, and its root password obtained by unknown individuals. The hacker(s) dumped contents from the PerlMonks user database on that machine, data which is estimated to be current as of approximately September 2008.The exploit was published in a hacker e-zine published on July 28, and was brought to the attention of PerlMonks administrators later that night.
The published material included the passwords, email addresses, and "real" names of all of the members of janitors and Saints in Our Book. However, the hackers presumably obtained, and could distribute, the user info of all PerlMonks users — at least those existing as of last September.
As far as is known, the main PerlMonks servers have not been hacked.
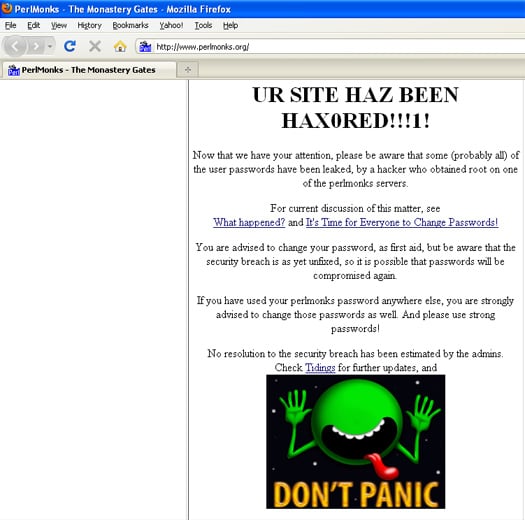
An earlier notice on PerlMonks' website (below) shows that the sense of humour in its cloisters remains strong and unimpaired, in spite of last week's security snafu. PerlMonks said it plans to begin using encrypted password hashes (something it ought to have been doing already, you might think). The site has reset the passwords of those users who haven't had a chance to change their login credentials themselves.
PAUSE for thought
The password security issue at PerlMonks has implications beyond one particular web site. An email from administrators of the Comprehensive Perl Archive Network (extract below), which maintains an archive of software written in Perl, warns of possible knock-on effects from the PerlMonks hack.
This email is being sent to inform you that all passwords on the popular PerlMonks website were compromised. Many CPAN authors have accounts there and in some cases have used the same password for PAUSE.If you have any reason to suspect that your PAUSE account password is no longer secure, please visit https://pause.cpan.org/ and change it.
PAUSE (Perl Authors Upload Server) is a system that allows registered users to upload new modules of code. Any problems there would be far more serious than breaches of an account on the community website PerlMonks alone.
The whole incident emphasises the need for robust password security. Using passwords that are resistant to dictionary attack - and that vary between different sites - is a good start along this road. ®
Bootnote
Thanks to Register reader Jacqui C for alerting us to the wider implications of the attack on the PerlMonks monastery.
