This article is more than 1 year old
Intel X25-M 34nm Flash SSD
The chip giant's second-gen solid-state drive
Review Intel was the first company to deliver a Sata SSD, its 80GB X25-M, and we were blown away by the combination of speed and silence. Unfortunately, the price was rather steep but you can’t make an omelette without breaking eggs.
When we reviewed the X25-M, it never occurred to us to ask about the fabrication process that Intel used to make the multi-layer cell (MLC) Flash memory chips. We were presented with that information when Intel launched the second-generation of X25-M drive. It turns out that the original process was 50nm and the new chips use a 34nm process.
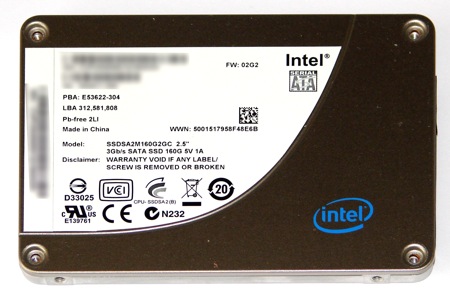
Intel's X-25M: slimmer, more capacious and cheaper
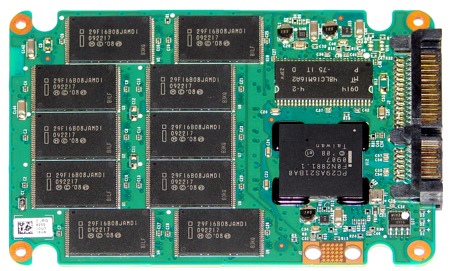
Inside the casing, the layout of the second-gen X25 looks similar to the first edition, but when you take a closer look you can see that all of the major components have been changed.
The single chip of cache memory has been increased in capacity from 16MB to 32MB, although the clock speed seems to have been reduced. The model code of the controller chip has been updated from PC29AS21AA0 to PC29AS21BA0, presumably to interface with the new Flash memory. The 1G drive used 20 chips to deliver the 80GB capacity, which works out to 4GB per chip.
With 2G SSD, the 80GB drive has ten 8GB chips on the same side of the PCB as the controller and cache with nothing on the back side of the board. The new layout suggests that a 160GB version should be a doddle and a 320GB drive would only require one spin of the memory technology.
34nm Flash chippery
The difference in specification between 1G and 2G is surprisingly small despite the change from 50nm to 34nm technology. The headline figures for sustained sequential read and write speeds are unchanged at 250MB/s and 70MB/s, respectively. The latencies have dropped from 85µs read and 115µs write to 65µs and 85µs which doesn’t sound like it will be very significant.
