This article is more than 1 year old
Google Chrome extension bars domains from search results
Your very own webspam blacklist (that you share with Google)
Google has released an experimental Chrome extension that lets you automatically remove individual domains from Google search result pages.
The extension is also a way for the company to gather information about undesirable domains as it works to combat so-called webspam. When you block a site, the extension notifies Google, and it may ultimately use this information to tweak results across its search engine.
Following a spate of stories criticizing the quality of its search results, Google has made a rather public effort to reduce webspam. In late January, it released a search algorithm change designed to demote certain sites that lift content from other sources, and the new Chrome extension takes aim at similar domains.
"We’ve been exploring different algorithms to detect content farms, which are sites with shallow or low-quality content," reads a blog post from Google anti-webspam man Matt Cutts. "One of the signals we're exploring is explicit feedback from users."
After you install the new extension, it adds a link just below each Google search result that lets you block the domain in question. When links are subsequently blocked, Google displays a message at the bottom of its search results page indicating as much, and it includes a link that lets you instantly reveal what was blocked. Naturally, after blocking a domain, you can unblock it. And when you do so, this information is set back to Google as well.
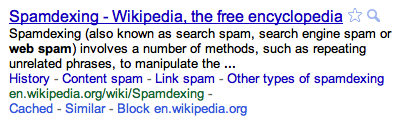
Google Personal Blocklist extension in action (see "Block" option at bottom)
The extension is called Personal Blocklist, and you can grab it here. It's speaks English, French, German, Italian, Portuguese, Russian, Spanish, and Turkish. If you block The Register, we will find you and we will kill you. ®
