This article is more than 1 year old
The Osborne 1: 30 years old this month
We remember the first commercial portable PC
Foxed by Vixen
Games and applications helped, but it was its portability that sold the Osborne 1. The machine had racked up sales of 11,000 units by the end of 1981.
If Osborne was the first company to develop a portable computer, it was also the first technology business - the first to lend its name to the phenomenon, at least - to accidentally commit suicide by announcing new products too soon.
Tell punters there's something much better just around the corner and they'll stop buying the current model, killing your company - a situation now called the Osborne Effect.
Or so the folklore goes. Osborne announced the follow-up to the Osborne 1, the Osborne Executive, in late 1982, but it didn't ship until May 1983. It had a bigger, 7in screen than its predecessor, but also an even bigger price: $2495. It was too much - the Executive did not sell well.
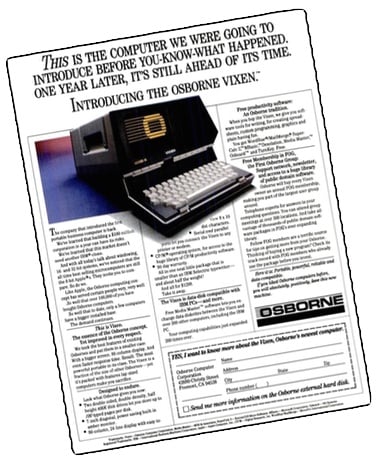
That didn't matter too much because the Osborne 1 was still selling well. Until Osborne announced the Vixen - aka the Osborne 4 - which steered potential buyers away from the Osborne. Demand plunged and even massive price cuts - the machine was pitched at just $999 in August 1983 - couldn't revive it.
Osborne Computer Company was declared bankrupt in September 1983. Osborne himself was ousted, but the firm lived protected from creditors by a court order. It finally showed off the Vixen in October 1984. It went on sale the following year, but by then World+Dog wanted IBM PC compatibles, and the Vixen wasn't. OCC closed down later that year. Osborne himself died in 2003. ®
Thanks to the many Osborne 1 and vintage computing fans who provided the ad scans.
