This article is more than 1 year old
Intel charges premium for Xeon E7 scalability
Socket to me, Westmere
Intel has refreshed its high-end x64-based server processors with the launch of the "Westmere-EX" chips, now known to the outside world as the Xeon E7s, and it wants some more money for them than you might have been budgeting.
In an indicator of the confidence that Intel has in its dominance of the x64 server racket, the company is not just charging a premium for higher core counts and faster clock speeds, which is to be expected. But the company is now charging a premium for the ability of a chip to scale the Xeon E7 processors across two, four, or eight processor sockets in a single system image.
Specifically, there are three different families of Xeon E7s. The E7-2800 series can be used in machines with two sockets, while the E7-4800s can be used in four-socket machines and the E7-8800s are used in eight socket-boxes. With the prior "Nehalem-EX" Xeon 7500 processors launched in March 2010, server makers could use the same chips in a machine with two, four, or eight sockets as they saw fit. There were eight different Xeon 7500 processors that had 4, 6, or 8 cores and that consumed 95, 105, or 130 watts of juice at various clock speeds and L3 cache sizes.
To appease supercomputer customers who wanted cheap two-socket nodes that had more memory scalability than is available in the Xeon 5600s, Intel crimped the Nehalem-EX line to create three different Xeon 6500 chips. Intel also had two chips - the Xeon E7530 and E7520 - that could not be used in eight-socket boxes.
This idea of bifurcating the high-end Xeon lineup is no longer not an experiment for a niche market, but a formal strategy for the wider commercial space. Well, it is actually trifurcation, if you want to be technical.
The premium for socket scalability is not huge, but will presumably bring Intel extra money as its server partners use Xeon E7 machines to try to dislodge proprietary mainframe and midrange systems and RISC/Itanium boxes running Unix and OpenVMS. And, that extra dough will help make up for aggressive pricing that Intel has set for many of the Xeon E7 chips compared to their Xeon 7500 predecessors.
Take a look at the Xeon E7 lineup:
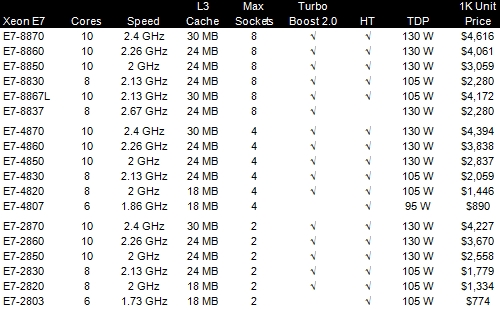
As you can see, the Xeon E7s come with six, eight, or ten cores, depending on the make and model, with varying amounts of L3 cache per chip. If you have a two-socket box and you want a ten-core chip running at the new top-end speed of 2.4GHz, then the E7-2870 will cost $4,227 a pop if you buy in 1,000-unit trays from Intel. The same exact chip that is tweaked to scale to four sockets, the Xeon E7-4870, costs $4,394, a 4 per cent premium just to scale. And the E7-8800 costs $4,616, a 9.2 per cent premium over the base two-socket model to allow it to scale to eight sockets. With the prior Xeon 7500 lineup, the top-end part, the X7560, had eight cores, ran at 2.26GHz, and cost $3,692; it could be used in machines with two, four, or eight sockets.
In some cases, the most equivalent Xeon E7 chip for a low number of sockets is less expensive than its Xeon 7500 equivalent from last year. In other cases, you pay a premium. There is no simple pattern, so shop carefully. Intel will continue to sell both processors, and they are socket compatible as well.
10 cores, 20 threads, 40 per cent more oomph
Like other Xeon chips coming out this year, the Xeon E7s are fabricated using Intel's 32 nanometer processes, a shrink from the 45 nanometer processes used with the Xeon 7500s last year. That shrink is what allows Intel to cram two more cores on the chip, but as El Reg speculated based on details Intel released at the ISSCC chip conference back in February, it looks like the Xeon E7s were designed to sport twelve cores and two of them were cut off the bottom to fit on the die. Check it out:
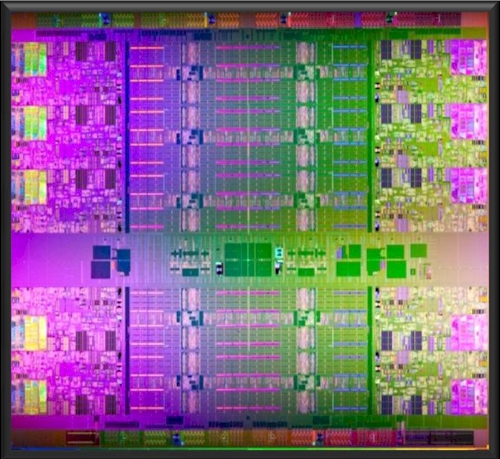
The Xeon E7 was designed at Intel's Bangalore, India chip lab. The Xeon E7 has 2.6 billion transistors and is 513 square millimeters in size. The chip uses a ring bus to connect cores and their L3 caches together so they can share work and data. This ring approach will be used across Xeon and Itanium processors, including the future "Sandy Bridge" Xeon E5s coming out later this year for two-socket and four-socket servers and the "Poulson" Itaniums due maybe next spring or so.
