This article is more than 1 year old
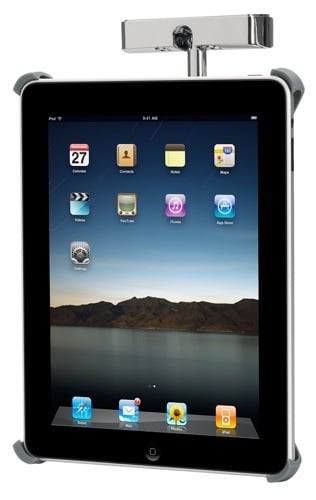
Griffin Cabinet Mount for iPad
Kitchen tablet
Txt Take Daily product reviews in 140 characters...
Griffin Cabinet Mount Pictures



Want our Txt Take on your gadget? Just send it in to Reg Hardware - details here.

Griffin Cabinet Mount for iPad
Easy to assemble, but bolt tightness governs pivot movement, so hinges may work loose with use. Not a tight iPad fit, unless tablet is cased
Price:
£50
RRP
