Android App of the Week Not an app dedicated to the vicissitudes of India’s currency or an equivalent of Grindr for fans of watersports. No, RunPee is an app designed to tell when the best time is to dash out of a cinema auditorium and take a quick tinkle, without missing too much of the action.

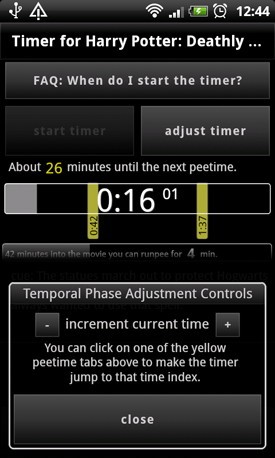
Films by date, name or search with an adjustable timer for late arrivals
The nuts and bolts of the app are as simple as the act of passing water. Choose a film and you are presented with a selection of time slots all long enough for a quick whizz but timed so you won’t really be missing anything by staring at the porcelain rather than the silver screen.
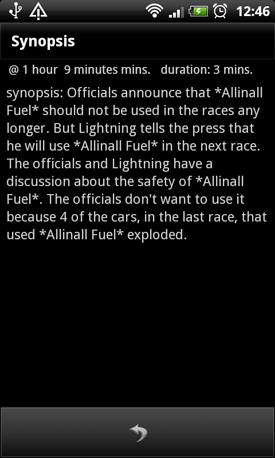
If you have a free hand you can also read a brief summary of what’s going on while you are actually micturating. Obviously if you are a bloke this increases the possibility of you dropping your phone into the urinal, so keep a firm grip.
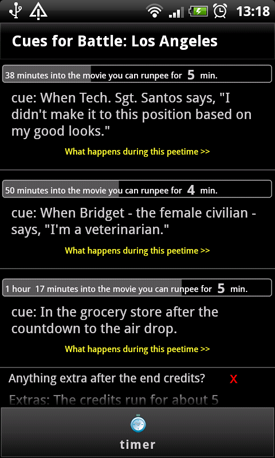
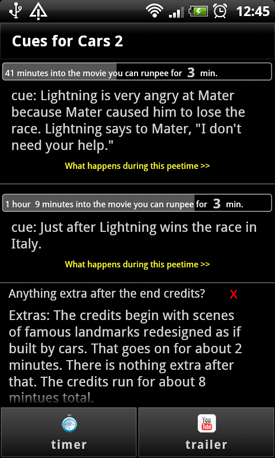
Cue points and the all important question: stay for the credits or get a beer>?
Each piddling opportunity has it’s own cue, so if you need to wee during Battle: Los Angeles – arguably a better use of time than watching that load of bunkum – just wait until Michelle Rodriguez says “I didn’t make it to this position based on my good looks” and have it away on your toes to the can sharpish for five minutes of blessed relief.
A feature soon to be added will make your phone buzz when you get to the next pee point so you can make a quick break for the john without the need to memorize dialogue cues or light up your phone screen and literally piss off everyone sitting behind you.
Timing a quick splash ‘n’ dash isn’t all the app is good for because it also tells you if there is anything worth seeing during or after the end titles – useful if you are trying to make last orders or have been holding it in for an hour and a half.

What you missed plus Twitter reviews and YouTube trailers
If you are late out of the bar before showtime there is also a synopsis of the first five minutes of each film so you can quickly catch up with anything you missed while draining your pint or bladder.

One small drawback in the need to have Adobe Air installed on your phone, adding the best part of 6MB to the instal, but at least Air can be shunted onto your SD card, as can the app itself. ®
Size 1.2MB
App2SD Yes

We make our choice of the best Android smartphone and tablet downloads every Tuesday. It you think there's an app we should be considering, please let us know.
More Android App of the Week Winners |
||||
 Dual File Dual File
Manager XT |
 Historypin Historypin |
 NASA NASA |
 Dinner Dinner
Spinner |
 ALK ALK
CoPilot Live Premium HD |

