This article is more than 1 year old
Hackers break SSL encryption used by millions of sites
Beware of BEAST decrypting secret PayPal cookies
Mozilla and OpenSSL: 'It's terrible, isn't it?'
Duong and Rizzo said the underlying vulnerability BEAST exploits is present in virtually all applications that use TLS 1.0, making it possible to apply the technique to monitor private communications sent through many instant messenger and Virtual Private Networking programs.
Although TLS 1.1 has been available since 2006 and isn't susceptible to BEAST's chosen plaintext attack, virtually all SSL connections rely on the vulnerable TLS 1.0, according to a recent research from security firm Qualys that analyzed the SSL offerings of the top 1 million internet addresses.
Chief culprits for the inertia are the Network Security Services package used to implement SSL in Mozilla's Firefox and Google's Chrome browsers, and OpenSSL, an open-source code library that millions of websites use to deploy TLS. In something of a chicken-and-egg impasse, neither toolkit offers recent versions of TLS, presumably because the other one doesn't.
“The problem is people will not improve things unless you give them a good reason, and by a good reason I mean an exploit,” said Ivan Ristic, Qualys's director of engineering. “It's terrible, isn't it?”
While both Mozilla and the volunteers maintaining OpenSSL have yet to implement TLS 1.2 at all, Microsoft has performed only slightly better. Secure TLS versions are available in its Internet Explorer browser and IIS webserver, but not by default. Opera also makes version 1.2 available but not be default in its browser.
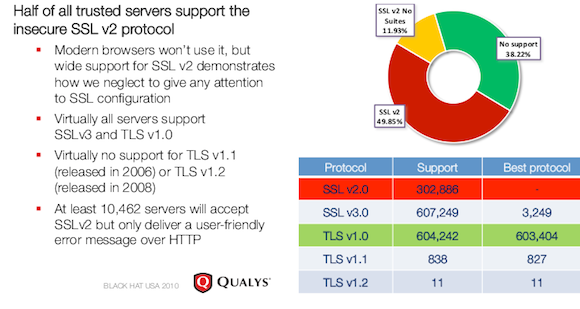
Support for TLS 1.1 and 1.2 is virtually non-existent, Qualys Director of Engineering Ivan Ristic says
Ristic, who presented his findings at the Black Hat security conference in August, has found additional evidence that websites often delay deploying upgrades that fix SSL security holes. His analysis found that as much as 35 percent of websites had yet to patch a separate TLS vulnerability discovered in November 2009 that made it possible to inject text into encrypted traffic passing between two SSL endpoints.
Researches said upgrading TLS is proving surprisingly difficult, mostly because almost every fix breaks widely used applications or technologies. A technology recently added to Google Chrome that significantly reduces the time it takes websites to establish encrypted connections with end-user browsers is just one example, said cryptographer Nate Lawson, principal of the Root Labs security consultancy.
Duong and Rizzo said there are many more examples.
"Actually we have worked with browser and SSL vendors since early May, and every single proposed fix is incompatible with some existing SSL applications," Duong wrote. “What prevents people is that there are too many websites and browsers out there that support only SSL 3.0 and TLS 1.0. If somebody switches his websites completely over to 1.1 or 1.2, he loses a significant part of his customers and vice versa.” ®
This article was updated to add details about the amount of time required to decrypt authentication cookies. It was also corrected to reflect the fact that Opera doesn't support TLS 1.2 by default. It was further updated to report the release of a new version of Chrome.
