This article is more than 1 year old
Apple's lone wolf approach to security will bite it in the rear
Everything's fine, can't hear you from the top of my cash mountain
Open... and Shut Apple may have minimal market share in desktop computers, but it has dominated the smartphone and tablet markets for years without any significant hacker exploits. Is Apple impervious to hackers, or is it just a matter of time before its luck runs out?
The answer to both questions is a definite maybe.
For years Apple has flown under the radar of serious hackers, its sub-10 per cent market share in personal computers is a weak target compared to Microsoft Windows, which roughly has a 90 per cent market share.
As Apple's slice of the personal computer market nudges up, now scraping 12 per cent, it is becoming an increasingly juicy target.
Still, it's doubtful that the Apple Mac will ever come to dominate the PC industry in a way that will encourage hackers to stay up late thinking of ways to crack it. Not only is the payoff relatively small but the amount of effort is comparatively large. Mac OS X, built on top of a security-conscious Unix kernel, is architected for security, whereas Windows has traditionally treated security as a feature to be added to the kernel, rather than baked right in.
While Microsoft's security has improved over time, Apple has long benefited from treating security as a first-class citizen in its engineering philosophy.
This carries through to the design of Apple's mobile operating system iOS, as well. It had better, as the top target for hackers going forward isn't Microsoft. It's Apple.
Imperva has been tracking hacker forums for years, and recently highlighted [PDF] the trend toward discussions about mobile, particularly iOS:
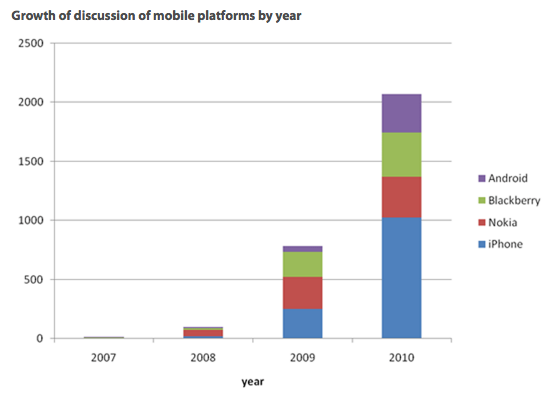
What hackers are chortled about among themselves
Apple, which was somewhat blasé about iOS security early on, releasing the iPhone with serious security design flaws, has since smartened up about mobile security. The company released a white paper [PDF] documenting Apple's iOS security approach in May 2012, and then tried and failed to convince hackers at the annual Black Hat conference that it takes security seriously.
And yet Apple continues to expose a sometimes casual approach to security, as recently highlighted by Mat Honan. In Honan's case, he admitted to failing to back up and secure his accounts sufficiently, but given Apple's emphasis on making beautiful devices for mainstream users, with equal or less attention to security, Honan's story could be played out again and again.
However, it's doubtful that hackers would bother to make the phone calls to Apple or Amazon in order to crack someone's accounts. Apple's security lapses involved social engineering on the hackers' part and the link between its devices and the cloud.
In terms of device-level and software-level security, Technology Review reports: "Apple's security architecture is so sturdy, and so tightly woven into its hardware and software, that it is both easy for consumers to use encryption on their phones and very difficult for someone else to steal the encrypted information."
Indeed, as much as I and others have criticized Apple for its obsession with controlling the end-user experience from software to silicon, this same approach may actually make its systems more secure than more open approaches.
Perhaps. It does seem that Apple software, be it Mac OS X or iOS, is much more resistant to security breaches than Windows ever was. But we're still in the early stages of mobile security, and it's very possible that as more hacker time and attention is devoted to Apple, Apple will crack. It certainly isn't immune to attack.
When iOS security does crack, a more open approach to security may be necessary. The last time Apple's security mechanisms were seriously compromised was the outbreak of the Flashback Trojan, which directly resulted from Apple taking a too-controlling approach to patching Java running on Macs. Microsoft, working closely with Oracle, issued security patches for its customers months before Apple got around to doing so.
Apple does things on its own timetable and how it chooses. But in the case of security, a willingness to collaborate with partners and even competitors may be the right way to go. ®
Matt Asay is senior vice president of business development at Nodeable, offering systems management for managing and analysing cloud-based data. He was formerly SVP of biz dev at HTML5 start-up Strobe and chief operating officer of Ubuntu commercial operation Canonical. With more than a decade spent in open source, Asay served as Alfresco's general manager for the Americas and vice president of business development, and he helped put Novell on its open source track. Asay is an emeritus board member of the Open Source Initiative (OSI). His column, Open...and Shut, appears three times a week on The Register.
