This article is more than 1 year old
Traceroute reveals Star Wars Episode IV 'crawl' text
'It is a period of civil war. A rebel network admin, striking from an IP address … '
A bored, snowbound network admin has made something lovely: a traceroute that produces the text of the opening crawl to Star Wars Episode IV - A New Hope.
Cisco Certified Internetwork Expert Ryan Werber, who blogs at Beagle Networks, says that during Boston's recent blizzards he decided to have some fun with DNS.
The result, depicted below, turns the usually-dull list of server names and/or IP addresses returned by a traceroute into some rather familiar text:
Werber says he pulled off the hack using the following technique:
“It is accomplished using many vrfs on (2) Cisco 1841s. For those less technical, VRFs are essentially private routing tables similar to a VPN. When a packet destined to 216.81.59.173 (AKA obiwan.scrye.net) hits my main gateway, I forward it onto the first VRF on the “ASIDE” router on 206.214.254.1. That router then has a specific route for 216.81.59.173 to 206.214.254.6, which resides on a different VRF on the “BSIDE” router. It then has a similar set up which points it at 206.214.254.9 which lives in another VPN on “ASIDE” router. All packets are returned using a default route pointing at the global routing table. This was by design so the packets TTL expiration did not have to return fully through the VRF Maze. I am a consultant to Epik Networks who let me use the Reverse DNS for an unused /24, and I used PowerDNS to update all of the entries through mysql.”
Werber says it took about 90 minutes to implement, which sounds like a better way to spend 90 snowed-in minutes than watching any of Episodes 1-III.
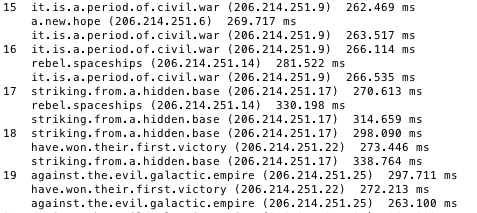
Tracert over to 216.81.59.173 and you'll get this rather amusing result
At this point Reg readers may grow tired of reading this, and want to know where is the rebel IP address?
It's on 216.81.59.173.
You may now continue with the operation and tracert when ready. Expect a few delays, as the rig Werber used wasn't set up to cope with mass traffic. ®
