This article is more than 1 year old
Four firms pitch hi-def DRM for Flash cards
Next-generation Secure Memory, anyone?
Panasonic, Samsung, Sony and Toshiba have begun licensing their new DRM technology for memory cards to anyone who feels the world needs yet another copy protection technology for HD content. They hope many content providers do indeed want a new DRM system, specifically one that secures content but doesn’t prevent content consumers from moving files from device to device, and even lending content to others.
This is a square consumers have wanted to see circled for some time. For most folk, the real flaw with DRM is not copy prevention but the way the technology ties content to specific devices or platforms. A movie downloaded from Apple’s iTunes can’t be played on a TV without the presence of extra Apple-made kit, for instance, and it certainly can’t be copied to an Android tablet or a Windows phone.
Transferring the file directly to a friend’s PC or to an intermediate location such as a network-attached storage device is easy, but the film can’t be viewed unless the viewer signs into iTunes in the guise of the original downloader, which requires an internet connection, at least at the time for signing in.
Panasonic, Samsung, Sony and Toshiba claim their system overcomes all these limitations. The technology is called SeeQVault (SQV) and it’s being touted by the Next Generation Secure Memory Initiatives - NSM for short - a firm founded by the aforementioned four to license their jointly developed DRM scheme. SQV was originally backed by SanDisk too, but it has since pulled out, according to NSM’s list of members.
NSM and its parents see SQV as a means of enabling SD cards and other Flash-based storage - though they also see a role in hard drives and other, more traditional forms of storage - as secure and portable file stores of licensed content, whether it’s material downloaded from an online shop or even ‘taped’ off telly on a DVR.
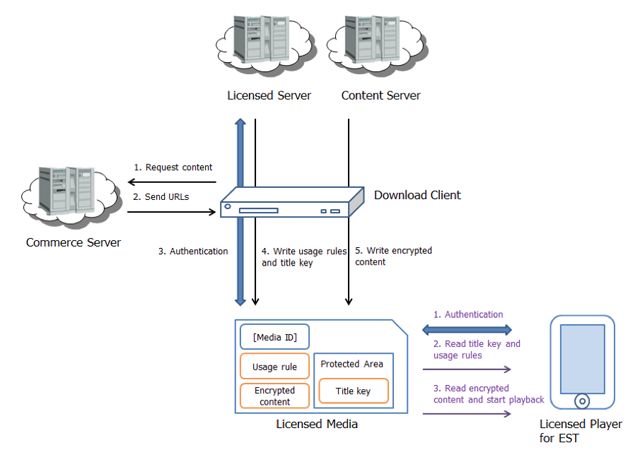
Secure download storage
Source: NSM
The notion is to make it easy for punters to move content around from device to device at will, while at the same time making the material stored impossible to rip, to keep the content providers happy.
“SQV-enabled memory and devices will allow the storage and playback of premium HD content across multiple devices with or without internet connectivity,” claims NSM. “With SQV-enabled Flash drives, SD cards, HDD and other media, consumers will be able to move HD content across their various devices in a secure key-managed environment that provides dynamic flexibility for content consumption while offering superior intellectual property protection.”
In plain English, that means a copy protection mode that keeps content secure without unreasonably limiting where and when the encrypted content is moved to. NSM’s approach is to lock the content to the medium rather than the host devices, allowing you to lend a friend a film to watch, just as you might pass them a DVD or Blu-ray, but in a way that prevents them from copying the content to keep. Flexible playback, which still requires player apps to be equipped with suitable authentication keys, and no need for online authentication should also calm fears about that other aspect of DRM: that content providers can stop you accessing content you’ve legitimately acquired.
NSM specifies two content storage formats: MP4 for discrete audio and video entities - copied downloads and ‘pre-recorded’ content - and MPEG 4 TS (Transport Stream) for recording content on DVRs and such. When the resulting file or data takes up more space than a storage device’s file system allows - for example, FAT 32’s 4GB limit - NSM advocates segmenting the content into multiple files.
A device doesn’t need to support NSM natively to play back licensed content, but if it doesn’t it has to be able to host third-party apps that are. This, says NSM, also makes the format a candidate for distributing ‘pre-recorded’ content - say a digital copy of a movie you’re buying on Blu-ray, there in the box. Or to allow SD to be pitched as an alternative to optical disc formats, whether bought off the shelf or spat out to order by a vending machine.
A card’s controller IC and its memory both need separate, unique NSM Secure IDs which are applied to the storage at manufacture, along with the media key information. These IDs and keys are combined and sent through the “secure authenticated channel” to the host and only when they are confirmed as legitimate can playback begin.
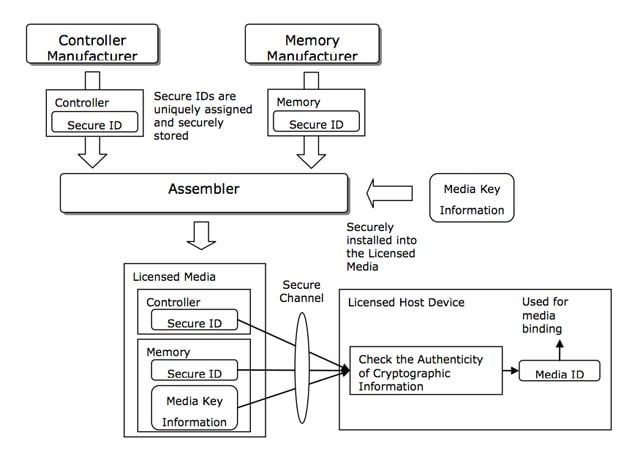
Layered security
Source: NSM
“Our multi-layer security system provides a more robust anti-cloning technology against unauthorised copying than existing content protection systems,” the NSM claims “By means of the secure authenticated channel, any malicious alteration of the information is prevented. The Secure IDs retained in the Licensed Media are managed only by trustable entities. Any sensitive information is never disclosed to non-compliant and non-trusted entities in the transaction. Furthermore, cloned media cannot be produced even by the information which a compliant Licensed Host Device can retrieve.”
Since much of the content set to be stored on NSM-compatible storage will come from the internet, it’s not unreasonable to wonder why the content industry needs NSM when initiatives like UltraViolet aim to deliver content usage flexibility through download and streaming, and by enabling multiple ownership of a single piece of content.
NSM argues that there’s still a window for physical media. Cloud-based streaming services are, it reckons, a few years away at least, especially for HD content to be consumed on the move. The capacity of mobile networks is too low and the cost too high for most punters to stream HD content by that path. The result, says the NSM, is an ongoing need for storage media capable of securely holding downloaded premium content.
Indeed, it says, NSM technology provides a secure storage for files downloaded from services like UltraViolet, useful for years before mobile networks and broadband can happily cope with a colossal number of HD streams and we don’t need to bother downloading anything any more.
Of course, it will be some time before we can see whether NSM DRM is as consumer-friendly as the company claims it is - or, indeed, whether it’s as secure as it’s promised to be. There will certainly be plenty of techies to put it security to the test. NSM has only just made its technology available for licensing, and there’s not yet any NSM-compatible storage out there. Toshiba has promised 16GB and 32GB NSM-compatible Micro SD cards. While these will be available in sample quantities at the end of next month, the company may not bring them to market until the end of 2013. ®
