This article is more than 1 year old
Malware linked to Chinese hackers aims at Japanese government
Spear-phishing threat from same locale as Google attacks
Malware researchers at Seculert say they've found two more cases of highly targeted malware coming out of China, and claim to have back-traced it to the same geographical region that was fingered as the source of the Project Aurora attacks.
"It's using a similar MO – infected PDFs sent out as part of a spear-phishing campaign," Aviv Raff, CTO of Seculert, told The Register. "We resolved it and found it was reporting to an IP address in China with the same physical location as the previous attacks. They are up to something."
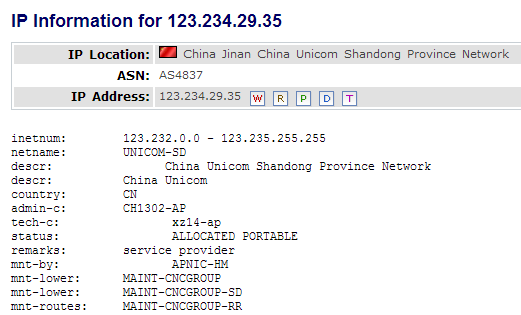
One of the malware samples was found to communicate with Japanese government websites, seemingly from a location in Korea. However, on Tuesdays between 8am and 7pm (local time) the malware would contact the IP address 123.234.29.35, which is found in Jinan, the capital of the Shandong province of China.
Once the malware got in contact with the new server it would attempt to download a new payload. Raff said this malware exploited a recently patched Java flaw and arrived in the form of an email with an attachment.
Jinan has long been fingered as a source of the spear-phishing attacks that were aimed at Google and other businesses as part of the attacks dubbed Project Aurora. Google was so put out by the attacks that it pulled out of the Chinese mainland and relocated to Hong Kong.
Do all roads lead to China?
In the interests of fairness, it should be pointed out that Jinan is a big place, with lots of universities full of mischievous young pranksters who might enjoy hacking Chain's traditional enemy. But the area was also identified as the location of hacking squads apparently linked to the People's Liberation Army in last month's Mandiant report into the New York Times attack.
"The ISP killed this time bomb by blocking the malware from reaching its target server, but based on the evidence from this we're going to be taking a much more in-depth study of this kind of targeted malware from China," Ruff said. ®
