This article is more than 1 year old
New York Times, Twitter domain hijackers 'came in through front door'
'Syrian Electronic Army' claims responsibility, registrar fingered as vector
Updated Hacktivist collective the Syrian Electronic Army (SEA) – or someone using its name – has claimed responsibility for hijacking the Twitter.co.uk, NYTimes.com and HuffingtonPost.co.uk web addresses.
At the time of writing, many of the domain names the SEA claimed to have seized were back under their owners' control. In some cases, only the contact details for the domains were altered.
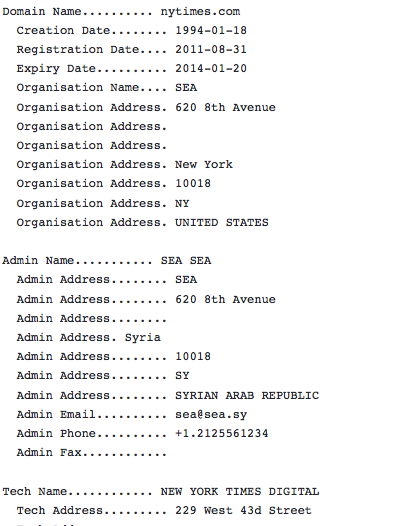
However, the records for nytimes.com and Twitter.co.uk pointed to addresses of nameservers operated by the SEA: effectively allowing the miscreants to redirect tweeters and NYT online readers to any site of the hackers' choosing.
The internet's domain name system (DNS) works by converting human-readable addresses, such as www.theregister.com, into network IP addresses that computers use to talk to each other. By altering the DNS records, attackers can cause havoc by ushering potentially sensitive web traffic to malicious systems (which is why using HTTPS is important).
Below are the hijacked DNS records for nytimes.com and twitter.co.uk last night:
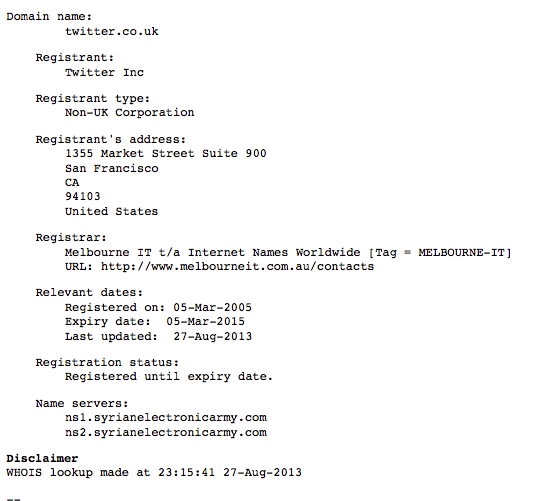
The attack actually hit an Australian domain registrar of which both Twitter and the Times were clients: Melbourne IT.
The New York Times attributed an outage last night to malicious activity; its workaround made it clear that a domain redirect was the problem since it pointed readers at its IP address to get directly to its site, sidestepping the domain-name system.

Twitter users were quick to blame the problems to domain-name registrar MelbourneIT, which is common to many of the hijacked domains. HD Moore of Metasploit Framework fame told Mashable that “if the attackers have found a weakness in the MelbourneIT system”, then other domains would also be at risk.
The New York Times also attributed the attack to MelbourneIT:
“The New York Times website was unavailable to readers on Tuesday afternoon following an attack on the company’s domain name registrar, Melbourne IT. The attack also required employees of The Times to stop sending out sensitive emails”, it has told employees.
The Register has tried to contact MelbourneIT, so far without success. ®
Updated to add
While MelbourneIT has yet to return calls from Vulture South, it has apparently told Business Insider a reseller was responsible for the hijack blunder.
Theo Hnarakis, chief executive of the web hosting biz, told Australian Broadcasting Corp radio today that hackers had modified the New York Times' domain using a partner's username and password.
"They came in through the front door," AP reported Hnarakis as saying. "If you've got a valid user name and password ... the assumption from our systems is that you are the authorised owner and user of that domain name."
Its statement is below.
The credentials of a Melbourne IT reseller (username and password) were used to access a reseller account on Melbourne IT’s systems.
The DNS records of several domain names on that reseller account were changed – including nytimes.com.
Once Melbourne IT was notified, we:
- changed the affected DNS records back to their previous values
- locked the affected records from any further changes at the .com domain name registry
- changed the reseller credentials so no further changes can be made
We are currently reviewing our logs to see if we can obtain information on the identity of the party that has used the reseller credentials, and we will share this information with the reseller and any relevant law enforcement bodies.
We will also review additional layers of security that we can add to our reseller accounts.
For mission critical names we recommend that domain name owners take advantage of additional registry lock features available from domain name registries including .com – some of the domain names targeted on the reseller account had these lock features active and were thus not affected.
The Register will post further updates as required. There are more technical details about last night's DNS hijack over on the CloudFlare blog. ®
