This article is more than 1 year old
WTF is ... 802.15.4e?
Very, very, low-power wireless to help Internet of Things nodes chat for a looong time
Among the causes of the serious bushfires that are still burning near Sydney, Australia, was a tree branch falling over a powerline.
Some Internet of Things (IoT) boosters suggest this kind of thing could be avoided by placing connected sensors just about everywhere so that news of a single failure could quickly trigger a useful action, in this case shutting down the live wire before it wriggles into a pile of dry leaves and ignites them.
The IoT could deliver that outcome and as we explained in this article some of the routing problems have been sorted out.
But before you can have the Layer 3 fun that article describes there's plenty to do lower down in the stack.
“We've got buckets of radio data standards,” you might say. “Why not just use WiFi or Bluetooth or something?”
The answer is electricity. The ideal sensor is one that can be deployed into the field and operate for years, rather than weeks. And, of course, in the sensor I just described, you want the power supply to be completely isolated from the electricity network it's monitoring.
That's why 802.15.4e is emerging as a key standard for the Internet of Things. So here, The Register is taking a look at some of the high points of 802.15.4e.
One answer to the low power requirements is simply to give individual sensors a throughput power rate than we've come to expect in consumer devices. We're accustomed to seeing channel throughputs in the hundreds of megabits per second on 802.11n devices. When 802.11ac ships that will rise even further. If you're willing to settle for a lower channel rate, you can reduce the transmitter power.
This, of course, isn't new, and neither is 802.15.4e. The base 802.15 standards were issued back in the previous decade, but were subject at the time to a certain amount of push-pull and jockeying within the IEEE. That left open the door to the much more familiar Bluetooth – also under the 802.15 umbrella – to become the world's favourite personal area network.
However, high-rate wireless isn't suitable for the world of sensor networks. Bluetooth's lowest-power class runs at 1mW (0 dBm). In the world of sensor networks, getting the power profile lower than that is an important aim.
Physical layer
Hence instead of the megabits or hundreds of megabits per second we're accustomed to discussing in the world of WiFi, the low-rate communications in sensor networks run between 20 Kbps and 400 Kbps (with an option to run things at a stunning 1 Mbps).
The protocol is fully acknowledged, because at lower power, there's a greater chance of error. The protocol also includes provision for shutting radio transmitters down, again to preserve power.
There are a number of radio channels supported, letting the sensor networks slot in wherever there happens to be spare space in different countries: 868-868.6 MHz, 902-928 MHz, 2400-2483.5 MHz, three bands in China (314-316 MHz, 430-434 MHz and 779-787 MHz), and 950-956 MHz in Japan.
Low power MAC layer
However, addressing the PHY layer with slower transmissions and lower power is only part of the picture. More is needed: the standard also needs to deal with MAC (media access control) layer behaviours that would, untouched, lead to wasted power.
Let's look, for example, at how the familiar 802.11 MAC layer works. It follows a scheme called CSMA/CA – carrier sense, multiple access / collision avoidance – and the basic pattern for a station wanting to transmit is:
- Choose a channel to transmit on, and listen to see if that channel is silent
- Send packet if the channel is idle
- If the channel is busy, wait until the channel is silent, and then wait a further random contention period
- If the channel is silent at the end of the contention period, transmit the packet.
The receiver will ACK each successfully received packet, and if there's no ACK, the sender will retransmit.
We all know that this works: there wouldn't be many Reg readers who haven't used WiFi at some point. But in the context of sensor networks, it's talkative, loud, and always-on – none of which is suitable for the sensor network. So the sensor network's MAC layer needs to preserve the battery, and needs to maintain that behaviour throughout the life of the device.
There's one more aim of the 802.15.4e extension – it's a good idea to avoid the need for central control of the network. If the network is built of sub-milliwatt radio sets, and it covers a large area, there will be a lot of individual devices that can't communicate with a centralised controller. Even if the controller is mains-powered and loud enough for everyone to hear, the distant nodes can't communicate back.
Coordinated Sampled Listening
This is handled by replacing the “traditional” wireless MAC layer with a scheme called Coordinated Sampled Listening, which basically lets the sensor go to sleep until it gets the radio equivalent of “wake on LAN” – a “Chirp” frame.
That's an important power saving, since some of the radio chips have sleep current at less than 2 micro-Amps, but can still wake up.
Since we're presuming there will be lots of sensors in the network, the Chirp frame has to be addressable. A receiver will start to wake up if it sees a Chirp, but will go back to sleep as soon as it realises “it's not my wakeup call”.
The Chirp frame says more than “wake-up”: it also sets a rendezvous time for a data transfer. The receiver will then go back to sleep until the rendezvous time. This scheduling allows the channel to be kept clear of traffic at the right time, rather than demanding the sensor go through the collision avoidance procedure.
Full function and reduced function devices
The standard also provides for two different types of MAC layer devices: the full-function device, and the reduced-function device. This allows a topology to be built in which the lowest-power devices can have their functionality cut, to save on power – and handily, the topologies available under 802.15.4e reflect the topologies we described when discussing routing for lower power networks. These are shown in the image below, courtesy of Cisco.
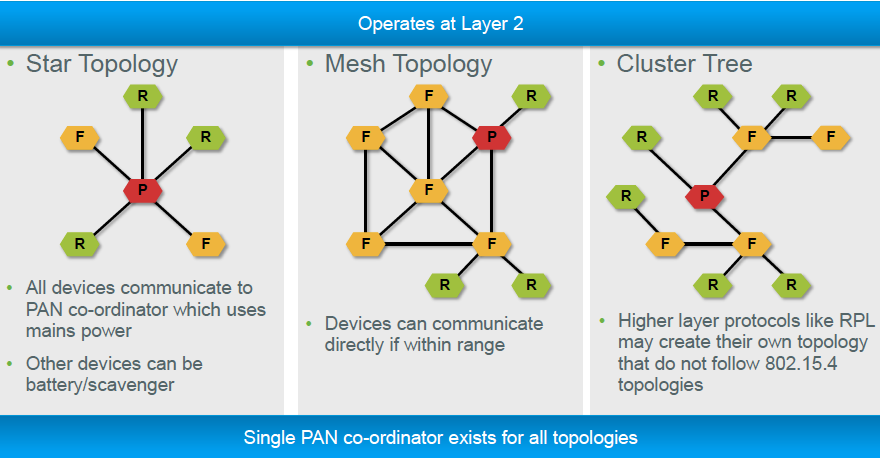
Image: Cisco
As the standard notes: “An RFD (reduced function device) is intended for applications that are extremely simple, such as a light switch or a passive infrared sensor; it does not have the need to send large amounts of data and only associates with a single FFD (full function device) at a time. Consequently, the RFD can be implemented using minimal resources and memory capacity.”
All networks, however, need a full-function device to act as coordinator.®
Bootnote: The Register appreciates the assistance of Cisco distinguished engineer Jeff Apcar for providing a background briefing on 802.15.4e.
