This article is more than 1 year old
Nexus phones carry SMS crash bug vuln
You have 1 new message: You've been p0wned
A Romanian security researcher has published a vulnerability that allows someone to crash a remote Nexus 4 or Nexus 5 phone – by sending them a crafted “Class 0” text message.
Instead of falling into a user's inbox and waiting for someone to read the message, a Class 0 or “flash message” pops up immediately as a message window that the user is supposed to decide whether or not to save.
On the Nexus phones, according to Levi9's Bogdan Alecu, the flash message is displayed above all active windows, with a semi-transparent overlay dimming them.
The bug that turns this into a vulnerability is this: Nexus 4 and Nexus 5 don't give audio notifications of incoming flash messages. So an attacker can pile message upon message on a victim until the phone begins to misbehave.
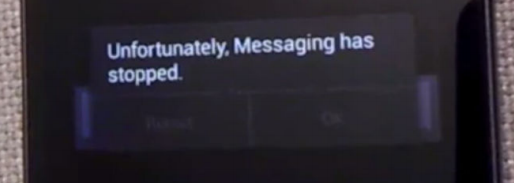
In this presentation to DefCamp 2013, Alecu identified various impacts of an attack in which more than 30 messages are sent to a target: either the messaging application crashes, or the phone reboots, or Internet access collapses.
If the victim's phone has SIM PIN-protection enabled, the phone will stop responding to the network.
Alecu complains that Google has known of the flax for more than a year with no fix announced. In the absence of an official fix, he points to this app, which is designed to act as a firewall against Class 0 messages. ®
