This article is more than 1 year old
Team Cymru spots 300,000 compromised SOHO gateways
Researchers spot attackers 'pharming' traffic with dodgy DNS
It's time to check the DNS settings on your broadband gateway, with security research group Team Cymru discovering an attack that could have redirected as many as 300,000 devices to a malicious resolver.
Once a gateway is compromised, the devices behind it would be sent to the attacker's DNS, exposing them to drive-by attacks, bogus bank sites, and other attacks.
The group's whitepaper says the attack exploits routers from TP-Link, D-Link, Micronet, Tenda and others.
In the case of TP-Link, a known cross-site request forgery attack appears to have been used, which allows attackers to inject a blank password in the device's Web interface. Some of the devices seen in the “SOHO pharming” attack seemed to have had their Zyxel ZynOS firmware replaced, again through a known vulnerability. Still others were probably compromised because users left weak default passwords in place.
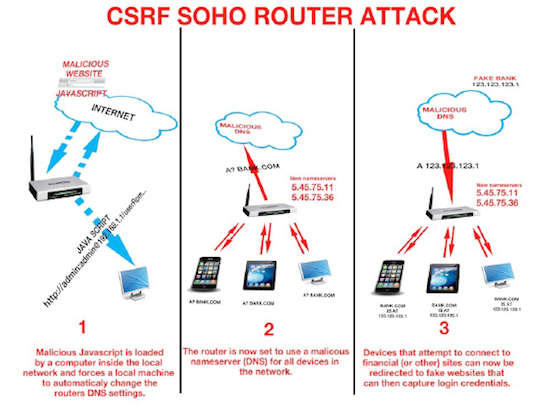
The CSRF attack. Image: Team Cymru
Target devices have their DNS redirected to 5.45.75.11 and 5.45.75.36. Team Cymru's estimate that there could be as many as 300,000 devices in the “SOHO pharming” network is based, it said, on unique IPs sending requests to those two addresses.
“Analysis of these malicious DNS servers revealed a wide range of compromised devices, including models from D-Link, Micronet, Tenda, TP-Link, and others,” the paper states.
While he greatest concentration of compromised kit was in “Vietnam, Italy, Thailand, Indonesia, Colombia, Turkey, Ukraine, Bosnia and Herzegovina, and Serbia”, the attack is global in scale, the paper states. Team Cymru adds that this appears to be a separate attack to the Linksys “Moon worm”.
The mitigation advice is to check devices' DNS settings, restrict or disable remote admin, and if possible, to block access to the attackers' DNS addresses. ®
