This article is more than 1 year old
Skiddies turn Amazon cloud into 'crime-as-a-service' – security bod
AWS is a growing haven for malware in survey of top web providers
Amazon Web Services' share of cloud-hosted malware-slingers has more than doubled in the last six months.
That's according to NTT subsidiary Solutionary, which revealed the finding in its Q2 2014 Security Engineering Research Team (SERT) report published on Tuesday.
The infosec researchers said that, out of the top ten ISPs and hosting providers surveyed, the proportion of malware-hosting websites served from Amazon infrastructure more than doubled from 16 per cent in Q4 2013 to 41 per cent in Q2 2014.
During the same period, net nasties on major European hoster OVH grew from 10 to 13 per cent; from 9 to 12 per cent on Akamai; and from 6 to 9 per cent on Google. GoDaddy, meanwhile, saw its share of malware decline from 14 per cent in Q4 2013 to 2 per cent.
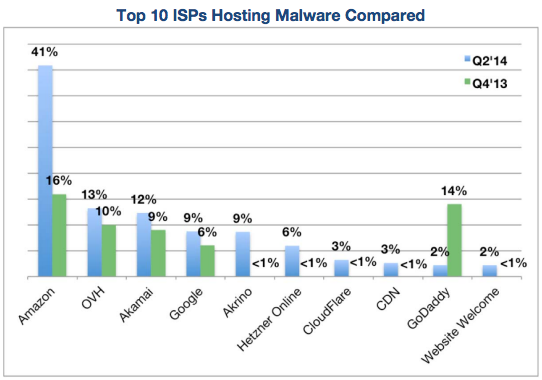
Behind bars ... Solutionary's stats for proportion of malware sites hosted by each provider, comparing Q4 2013 to Q2 2014
This isn't the first time Amazon has been used by miscreants to host large amounts of malware – Solutionary made the same claims in its Q4 2013 SERT dossier, and Kaspersky researchers discovered in 2011 that Amazon Web Services was playing host to the notorious SpyEye malware.
Part of the reason must be Amazon's scale and popularity as a cloud service, along with its Bezos-backed low, low prices. This means any wannabe hacker can buy server images from crooks and deploy them on AWS to build a network of malware-spreading websites.
"Cloud instances of web services are extremely simple to provision on Amazon, GoDaddy, and all the majors," noted Solutionary security gumshoe Chad Kahl in a chat with The Register on Wednesday.
"When you start going into the underground forums – the Russian forums, the Chinese forums – they don't just sell a Zeus malware package, they'll sell you an entire command-and-control infrastructure and a phishing website to set up, and a drive-by-download website to set up.
"You go to them and it's crime-as-a-service," he explained. "It's truly script kiddies on a major scale."
Another reason why large providers may be having trouble stomping out the script kiddies on their service is that the criminals are flitting rapidly between different clouds, Kahl said. "A lot of the malware operators bounce in between hosting providers, internet service providers and proxy hosts in different countries."
Digital fingerprints of the viruses, Trojans and other software nasties hosted in public clouds are known and circulated in the infosec world, and can be used to identify malicious binaries, Kahl noted.
"The question is can these providers put the infrastructure in to scan everything?" he asked.
Amazon and GoDaddy and Google and so on may be scrimping when it comes to investing in the tools needed to efficiently check the signatures of hosted files against databases of known evil binaries, he said.
"When we're talking about someone as big as Amazon or GoDaddy it would be a significant investment both in architecture and in time to go through and monitor everything as it's being put up – regular scans – to detect everything and take down these groups," the researcher said.
Some companies are making good moves, though, we're told, such as Microsoft which has a number of malware-splatting initiatives. Similarly, Google's new Project Zero team is tasked with hunting down vulnerabilities in software before they are discovered and capitalized on by crooks.
As for Amazon, a spokesperson told us: "AWS employs a number of mitigation techniques, both manual and automated, to prevent the misuse of the services.
"We have automatic systems in place that detect and block many attacks before they leave our infrastructure. Our terms of usage are clear and when we find misuse we take action quickly and shut it down. Companies that do see malicious activity originating from AWS should contact us immediately at ec2-abuse@amazon.com." ®
