This article is more than 1 year old
NEW, SINISTER web tracking tech fingerprints your computer by making it draw
Have you been on YouPorn lately, perhaps? White House website?
A new, persistent web-tracking technology developed has been used to track web users across many of the world's most popular websites, including those of the White House and even wholesale smut platform YouPorn.
The canvas fingerprinting technique was described in 2012 by University of California researchers (PDF) as a means to silently track the web sites users visit.
Surveilled users watched over by canvas attacks cannot defend themselves by clearing the tracking mechanism by normal browser flushing nor guard against infection using apps like AdBlock Plus.
It gets worse: researchers from the universities of Princeton and Belgium's KU Leuven have now found, and documented in a paper titled The Web never forgets: Persistent tracking mechanisms in the wild (PDF), that previously-unreported canvas fingerprinting scripts were deployed on 5000 of the top 100,000 most popular websites as rated by Alexa.
The lion's share of these were running thanks to the AddThis app under an experiment launched without the knowledge of the named websites.
Those sites included the Australian Government's Department of Foreign Affairs and Trade, the Department of Health and the Fair Work Ombudsman, Blighty's Ministry of Justice and the website for the Royals, along with scores of US Government sites including the White House.
Topping the list was the highly rated YouPorn.com website which came in with a rank of 108.
AddThis chief executive Rich Harris told ProPublica it began live experiments this year with canvas fingerprinting across some of the 13 million sites on which it appears as a means to replace traditional text cookies.
The news prompted a startled YouPorn to drop the AddThis function.
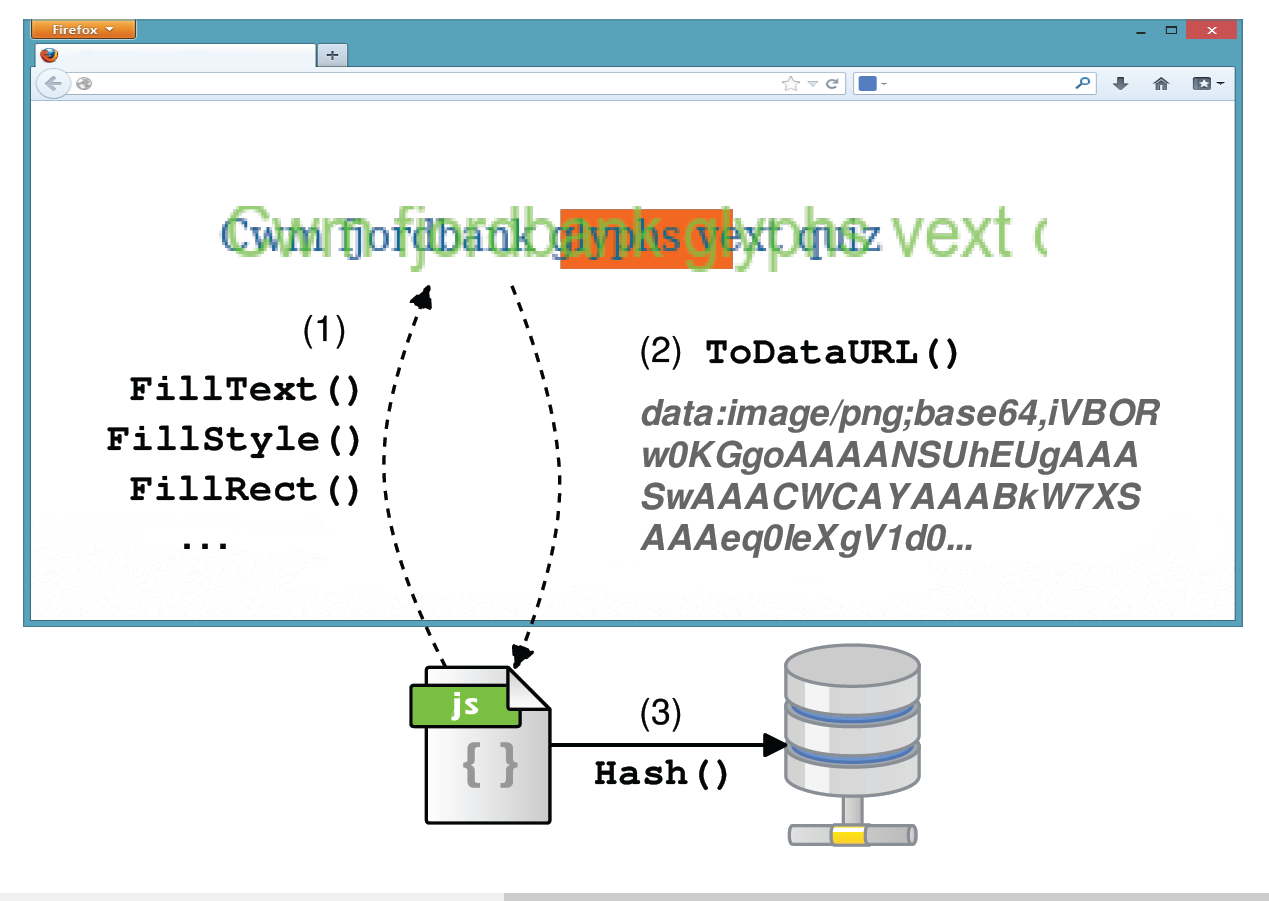
Canvas fingerprinting worked by making user web browsers draw unique images using the canvas API which was then converted into an identification number.
"The tracking mechanisms we study are advanced in that they are hard to control, hard to detect and resilient to blocking or removing," the six researchers wrote in the paper.
"Canvas fingerprinting uses the browser’s Canvas API to draw invisible images and extract a persistent, long-term fingerprint without the user’s knowledge."
Easy or stable blocking mechanisms have not yet been developed, however users could test the Chameleon experimental browser, run Tor or blacklist AddThis via NoScript or NotScript.
"A frequent argument in online privacy debates is that individuals should take control of their own privacy online [but] our results suggest that even sophisticated users may not be able to do so without significant trade-offs," they wrote.
The privacy crusaders also examined flash cookies including evercookies, which used slippery storage tactics and cookie syncing which skipped Same-Origin Policy.
They found the cookies in 10 of the 200 most popular websites and 107 of the top 10,000 sites. Of these 33 different flash cookies were detected including the new IndexedDB evercookie vector previously unseen in the wild.
Readers could find technical details of the research in the report by Gunes Acar; Christian Eubank; Steven Englehardt; Marc Juarez; Arvind Narayanan, and Claudia Diaz. They could also opt out of AddThis personalised tracking if they disagreed with the company's claims that targeted ads "enhances your internet experience" ®.