This article is more than 1 year old
Attackers raid SWISS BANKS with DNS and malware bombs
'Retefe' trojan uses clever spin on old attacks to grant total control of bank accounts
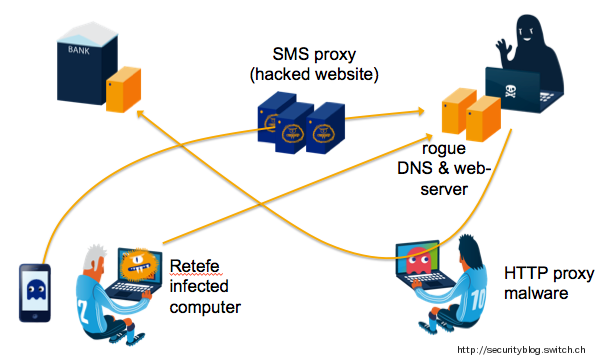
Attackers suspected of residing in Russia are raiding Swiss bank accounts with a multi-faceted attack that intercepts SMS tokens and changes domain name system settings, researchers have warned.
The attacks sported a clever implementation of malware that pointed victim machines to replica phishing bank sites when they attempt to access their accounts without triggering any warnings.
That tactic was accomplished by malware that manipulated a victims' DNS settings and installed an SSL certificate for the phishing sites before wiping itself clean to remove evidence of infection.
Users who fell for the email campaign and subsequently installed the malware would be prompted to install an Android app to purportedly secure their banking transactions, but which would serve to steal second factor SMS tokens and ferry it off to an attackers' command and control server or mobile phone number.
SWITCH CH engineer Daniel Stirnimann (@seckle_ch) said the "Retefe" banking trojan, as the attack is known, is impressively simple.
"After infection, the installation routine deletes itself from the compromised system which makes it difficult for anti-virus programs to detect the infection," Stirnimann wrote.
"The malware has an elegance that is difficult to beat: It does away with the [downloaded] software components and thus minimizes the complexity. It also seems that there is now an economic point of view from scammers to infect new victims' PCs via spam campaigns."
The Android software also stole a victim's mobile transaction authentication number, used for second factor authentication by European banks including those operating in Australia and New Zealand.
Stirnimann said scarcely-used mobile anti-virus tools should detect the application.
With the token in hand, attackers had "full control" of victim bank accounts which the logged in with a hacked local computer to avoid triggering anti-fraud mechanisms.
Researchers David Sancho, Feike Hacquebord and Rainer Link of security firm Trend Micro also pried apart the malware which they said in a report was the work of Russians using the handles -=FreeMan=- and Northwinds who have been active black hats since 2011.
Trend Micro dubbed the malware campaign "Emmental" after the delicious and hole-ridden Swiss cheese.®