This article is more than 1 year old
Leaked docs reveal power of malware-for-government product 'FinFisher'
Win 8 Pro tip: Govt spyware can't tap Skype's Metro app
A string of documents detailing the operations and effectiveness of the FinFisher suite of surveillance platforms appears to have been leaked.
The documents, some dated 4 April this year, detail the anti-virus detection rates of the FinFisher spyware which German based Gamma Group sold to governments and law enforcement agencies.
The leaks were posted to cyberlocker Dropbox by a parody Gamma Group Twitter account (@GammaGroupPR) that began posting links to the documents and satirical tweets today.
It proclaimed to the amusement of followers that the products were being sold to the general public because the company had "run out of governments to sell to".
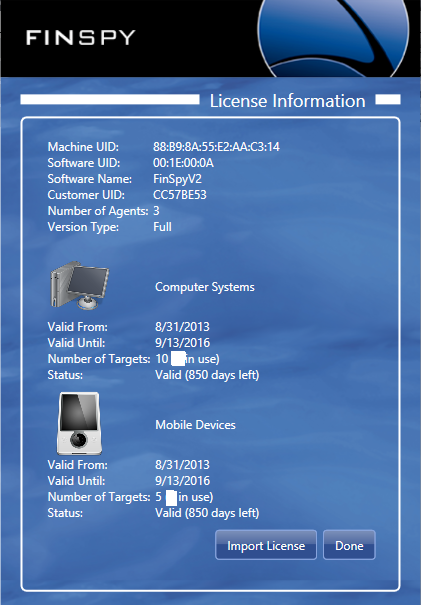
Gamma Group and the operator of the fake Twitter account did not confirm the legitimacy of the documents or whether the company was breached by the time of publication. However the documents did not appear to have been posted elsewhere and included a purported screen shot of a customer's FinSpy installation.
Information on Gamma Group's spy kit was last leaked to Wikileaks in October 2011 under the Spy Files. Since then the targeted malware offerings had become under fire from activist and privacy groups.
FinFisher's FinSpy
One spreadsheet titled FinFisher Products Extended Antivirus Test dated April shows how the software performed against 35 popular anti-virus products with most 'passing'. That means FinFisher would probably not be detected by a targeted users' security systems.
Another document detailing release notes for version 4.51 of FinSpy [pdf] also dated April show a series of fixes made to the products including patched to ensure the rootkit component could avoid Microsoft Security Essentials, that the malware could record dual screen Windows setups, and improved siphoning of emails through Mozilla Thunderbird and Apple Mail.
the dump also reveals Windows 8 users should opt for the Metro version of Skype rather than the desktop client because it cannot be tapped by FinFisher.
OS X Skype users would be alerted to the presence of FinFisher by a notification indicating that a recording module was installed.
A price list, which appeared to be a customers' record, revealed the FinSpy program cost 1.4 million Euros and a variety of penetration testing training services priced at 27,000 Euros each. The document did not contain a date but it did show prices for malware targeting the recent iOS version 7 platform.
Support costs ranged from 2218 Euros for USB malware support to 331,840 for fifth year support for FinSpy.
The leaked documents also included a FinSpy user manual and brochure. ®
