This article is more than 1 year old
Amazon REINTRODUCES Kindle swindle vulnerability
Malware gives book thief grief
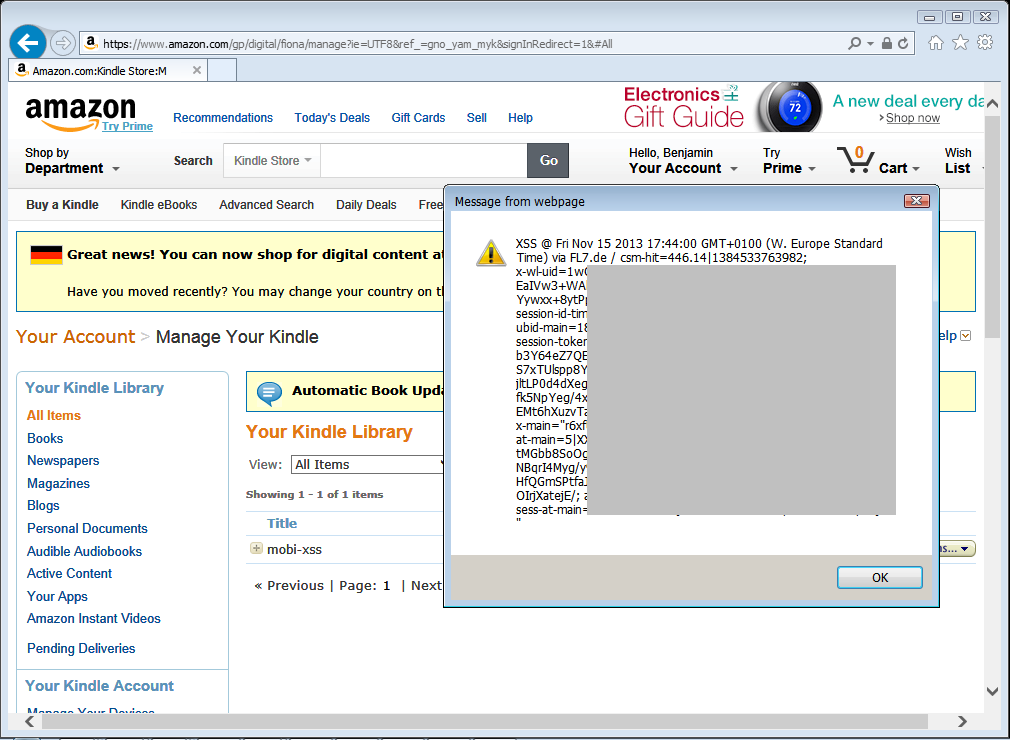
Amazon has reintroduced and again fixed a flaw into its Kindle management page that allows attackers to commandeer accounts by booby trapping pirated books, researcher Benjamin Mussler says.
The flaw was first discovered and fixed last October, when Amazon closed off the ability for bad guys to inject nasty script into eBook metadata. That code would execute when books were uploaded to the Sent to Kindle service, a tool that allows users to send documents to Amazon's e-readers.
Book pirates were obvious targets because they sought out *.mobi and *.awz books for download and shipped them off to the upload service.
Mussler said the flaw was re-introduced after an update to the Manage Your Kindle page.
"Malicious code can be injected via ebook metadata; for example, an ebook's title," Mussler said.
" ... the code will be executed as soon as the victim opens the Kindle Library web page. As a result, Amazon account cookies can be accessed by and transferred to the attacker and the victim's Amazon account can be compromised."
The bug existed for at least two months after Mussler discovered and reported the flaw 9 July. Amazon had not responded by Friday leading Mussler to drop the disclosure publicly.
Attackers could have crafted titles such as to a book title that would grant access to Amazon accounts.
Mussler said Amazon used his proof of concept attack code during its testing of the Manage your Kindle page and was surprised that an oversight allowed the flaw to be re-introduced.
The Cross Site Scripting flaw also affected popular free book management program Calibre but was fixed by contrast an impressive four hours after it was reported.
Attackers have been found targeting pirate book hunters on cyber locker sites using drive-by-downloads and malicious scripts. Pirate ebooks were also traded on public and private torrent trackers. ®