This article is more than 1 year old
Security seals clobbered ahead of Black Friday bonanza
Hackers' delight as vendors certify phishing sites
This Black Friday, beware the shop with the security seal: researchers have shown that issuers of common good webkeeping seals of approval sometimes miss basic flaws, happily certify phishing sites and inadvertently function as a hackers' black book of vulnerable sites.
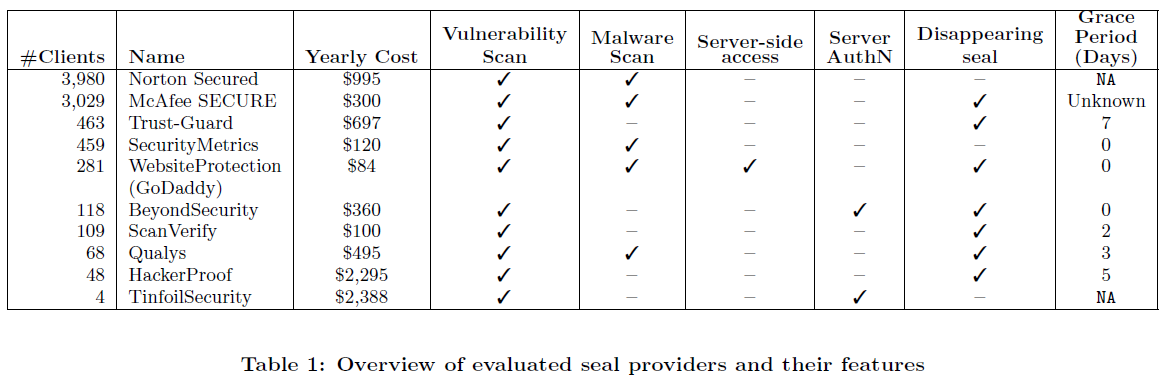
The research examined the effectiveness of the top 10 website security seals from the likes of Symantec, Tinfoil Security and McAfee which charge up to US$2388 a year to conduct automatic vulnerability tests and award a seal/logo for those which passed.
Lead author Tom Van Goethemz and colleagues Frank Piessensz, Wouter Joosenz from Belgian institution KU Leuven, plus Nick Nikiforakis of Stony Brook University, found seals were poor indicators of site security, could be easily tricked by lazy sysadmins, and even functioned as 'vulnerability oracles' for attackers.
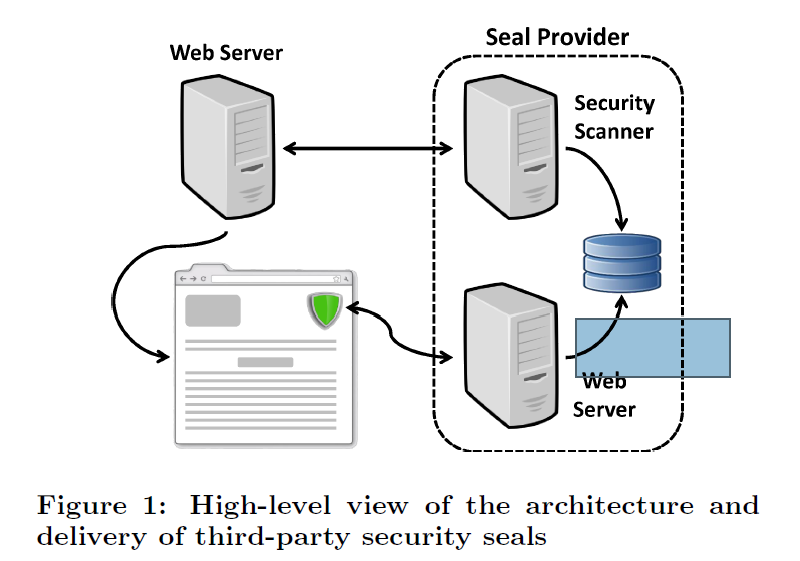
"Among other things, we show how seals can give more credence to phishing attacks, and how the current architecture of third-party security seals can be used as a completely passive vulnerability oracle, allowing attackers to focus their energy on websites with known vulnerabilities," they wrote in the paper Clubbing Seals: Exploring the Ecosystem of Third-party Security Seals [PDF].
"Through a series of automated and manual experiments, we discover a real lack of thoroughness from the side of the seal providers, which results in obviously insecure websites being certified as secure.
"... we show that, paradoxically, third-party security seals can assist attackers in identifying vulnerable targets, and even provide them with the exact vulnerability."
Seals are most often used by popular shopping sites; 74 percent of the 8000 tested were part of Alexa's top one million websites and a third of all examined were e-commerce sites.
The seals are designed to reassure security-conscious American consumers looking to snap-up bargains this Friday as part of the Black Friday online sales bonanza.
Security seals unraveled when tested by the researchers against a custom web application loaded with 12 known vulnerabilities, with the best seal program detecting less than half of the flaws.
All tested seals and vulnerability scanners - Acunetix, HP WebInspect and Burp Suite - failed to detect the common DOM-based and reflected XSS flaws.
Previous research that found seals wanting was focused on whether the technology resulted in higher increased sales and the authors claimed their work was the first to systematically evaluate the security of seals at scale.
Proposed defensive measures could help mitigate identified risks but nothing could remove the vulnerability oracle that the technology provided hackers as it was "central to the current architecture" and "appeared to not have a technical solution".
Of the 8000 examined, 333 websites temporarily lost the seal during the research while 189 never regained it most likely due to vulnerabilities.
Black book
While seals are a poor indictor of good website security, they work well as a means for hackers to identify vulnerable sites.
The term "vulnerability oracle" was coined after the team found hackers could sign up for a security seal trial and replay the evaluation checks against those sites where the certification had been dropped.
Worse, bad guys could obtain a website's security report by simply creating an account that granted them a url such as 'twitter.com/darrenpauli'. From there they could upload a file which due to file name validation failures affecting several seal vendors would be accepted as proof of site ownership.
Hackers inclined to phish this Friday could simply set up a phishing site for their preferred target and apply to any of the 10 seal slingers for certification of which each was happy to award provided security tests were passed.
But they need not even secure their sites: Attackers and "sketchy" sysadmins could run basic cloaking techniques and write two lines of configuration code that would bluff examinations by all tested security seal vendors.
".. we managed to circumvent the detection of vulnerabilities by rerouting all traffic originating from seal providers to a static web page," the researchers wrote.
"This, unfortunately, requires much less effort than continuously mitigating vulnerabilities, and could thus be employed by sketchy website owners who just want to convince their customers their website is secure."
They found little difference in the benefits between security-sealed and non-sealed sites based on nine attributes including HTTP Strict Transport Security, secure cookies, and Content Security Policy. The slight variation found non-sealed sites were more secure.
The team also found "textbook" SQL injection cross-site scripting flaws in seven of the paltry nine sealed websites which permitted the researchers to conduct penetration tests. ®