This article is more than 1 year old
Kiwi hacker 'menace' pops home detention tracker cuffs
Hack unit worn by on-parole crim. Blackmail said crim. Profit
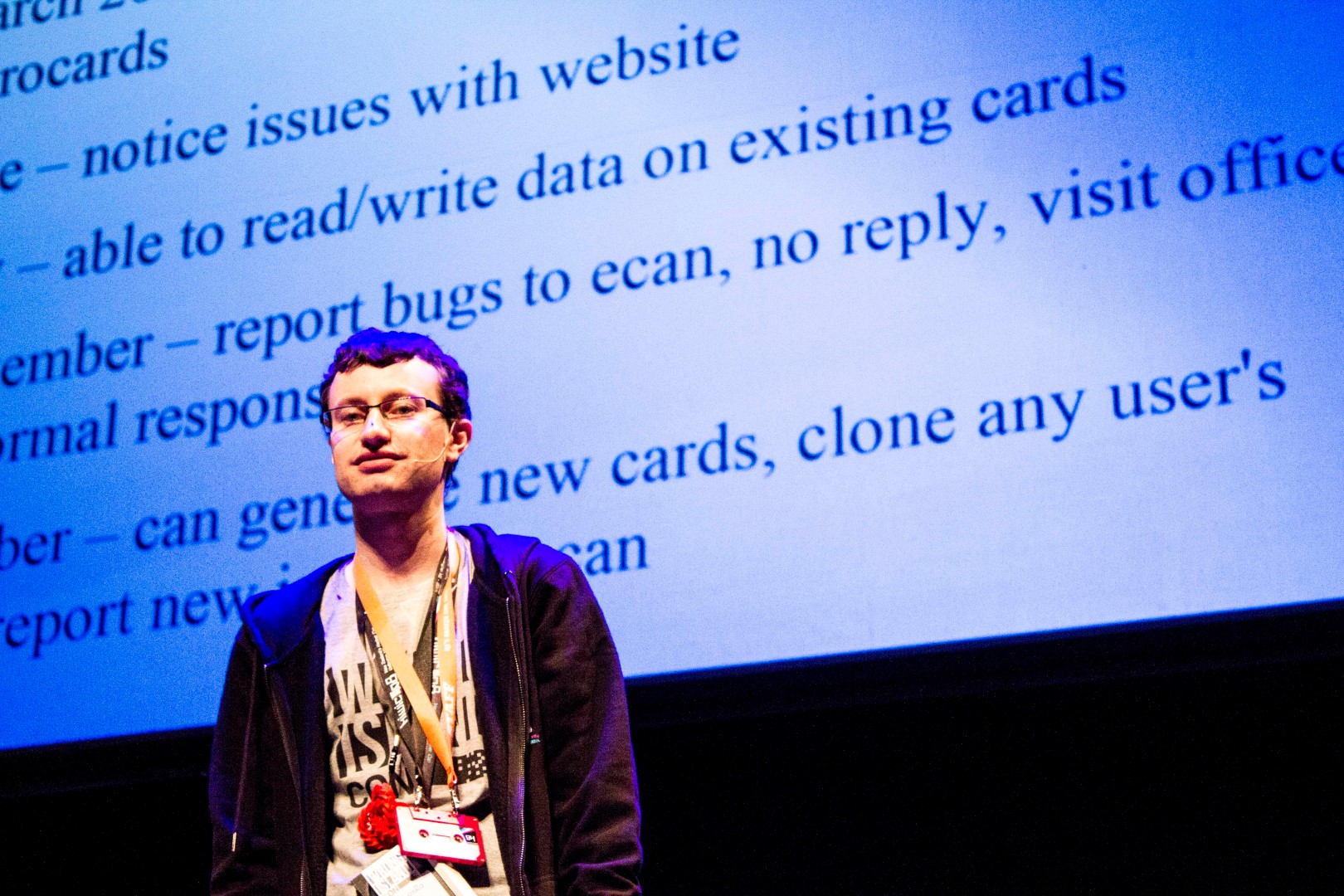
Kiwicon Christchurch bus hacker William Turner has demonstrated how to trick home detention ankle monitors used in New Zealand.
The monitor hack meant the location of criminals could be falsely reported to contractor G4S, triggering alarms.
The feat was a tool of mischief makers and blackmailers, Turner said, but importantly could not be used to allow criminals to give police the slip. Criminals spoofing their locations and attempting to leave their homes would still raise alarms.
Turner, described fondly by infosec peers as a "fu**ing menace", told the Kiwicon hacker meet in Wellington that his aluminium foil Faraday-cage attack worked against the multiple wireless communication mechanisms the monitors employ.
"A few ways you could monetise this could be in blackmailing criminals, saying that you'll spoof their location," Turner told amused delegates.
"You could go war driving looking for people, or maybe do spoofing as a service. Or do cyber-hits on people for a fee."
His talk followed a disclosure last year where he told the conference how to score free rides on the Christchurch bus system, a feat which earned him a police visit.
Beyond the absurdity of criminal blackhat extortion, the attack was largely an academic affair and had little use for criminals.
Further research was required to determine if criminals could disable sufficient checks to allow them to leave home without triggering alarms.
A series of absent technical checks meant Turner could employ location and SMS spoofing, and brute force password attacks to foil GPS and fail-over SIM communication.
The monitor tested was purchased from Taiwan and was said to be all-but-identical to those used in New Zealand, meaning both units were vulnerable to the NZ$500 spoofing attack. Similar units are used around the world. ®