This article is more than 1 year old
Your hard drives were riddled with NSA spyware for years
Kaspersky: 'Equation Group' attacked 'high value targets'
The US National Security Agency (NSA) infected hard disk firmware with spyware in a campaign valued as highly as Stuxnet that dates back at least 14 years and possibly up to two decades – all according to an analysis by Kaspersky Labs.
The campaign infected possibly tens of thousands of Windows computers in telecommunications providers, governments, militaries, utilities, and mass media organisations among others in more than 30 countries.
The agency is said to have compromised hard drive firmware for more than a dozen top brands, including Seagate, Western Digital, IBM, Toshiba, Samsung and Maxtor, Kaspersky researchers revealed. This is not beyond the realm of possibility: hacking custom code into disk controller firmware has been demonstrated.
On Monday, Reuters reports sources formerly working with the NSA confirmed the agency had infiltrated drive firmware; Kaspersky doesn't lay at the feet of the spy hive.
Kaspersky's analysis says the NSA made a breakthrough by infecting hard disk firmware with malware known only as nls_933w.dll capable of persisting across machine wipes to re-infect targeted systems.
Researchers said the actors dubbed 'The Equation Group' had access to the firmware source code and flexed their full remote access control over infected machines only for high value targets.
"The Equation group is probably one of the most sophisticated cyber attack groups in the world," Kaspersky bods said in an advisory.
"This is an astonishing technical accomplishment and is testament to the group's abilities."
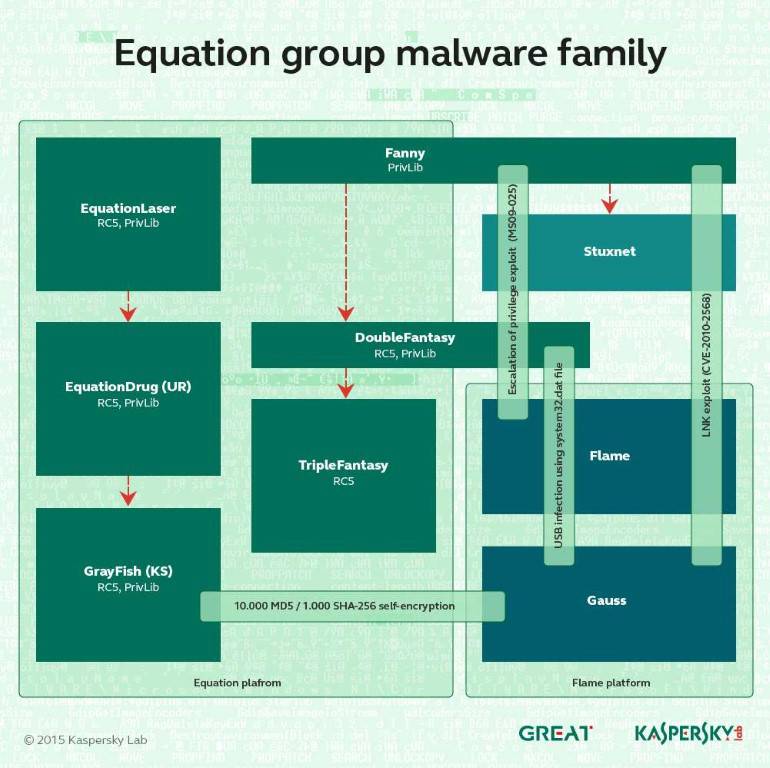
"For many years they have interacted with other powerful groups, such as the Stuxnet and Flame groups; always from a position of superiority, as they had access to exploits earlier than the others."
It called the campaign the "Death Star" of the malware universe, and said (PDF) the Equation moniker was given based on the attackers' "love for encryption algorithms and obfuscation strategies".
Reuters sources at the NSA said the agency would sometimes pose as software developers to trick manufacturers into supplying source code, or could simply keep a copy of the data when the agency did official code audits on behalf of the Pentagon.
Western Digital said it did not share source code with the agency. It was unknown if other named hard drive manufacturers had done so.
Vectors
The agency spread its spy tools through compromised watering hole jihadist sites and by intercepting and infecting removable media including CDs.
The latter vector was discovered in 2009 when a researcher using the pseudonym Grzegorz Brzeczyszczykiewicz received a CD sent by a unnamed prestigious international scientific conference he had just attended in Houston.
Kaspersky said that CD contained three exploits, of which two were zero day, sent by the "almost omnipotent" attack group.
Another method included a custom malware dubbed Fanny which used two zero day flaws identical to those executed later in Stuxnet.
Its main purpose, Kaspersky's researchers said, was to map air-gap networks using a unique USB-based command and control mechanism which could pass data back and forth from air-gapped networks.
This researchers said indicated the authors worked in collaboration with those behind the Natanz uranium plant weapon and further shored-up claims the NSA was behind the detailed attacks.
Other trojans used in the prolonged and wipe spread attacks were dubbed Equationlaser; Equationdrug; Doublefantasy; Triplefantasy, and Grayfish.
It detailed the trojans in a document:
- EQUATIONDRUG – A very complex attack platform used by the group on its victims. It supports a module plugin system, which can be dynamically uploaded and unloaded by the attackers.
- DOUBLEFANTASY – A validator-style Trojan, designed to confirm the target is the intended one. If the target is confirmed, they get upgraded to a moresophisticated platform such as EQUATIONDRUG or GRAYFISH.
- EQUESTRE – Same as EQUATIONDRUG.
- TRIPLEFANTASY – Full-featured backdoor sometimes used in tandem with GRAYFISH. Looks like an upgrade of DOUBLEFANTASY, and is possibly a more recent validator-style plugin.
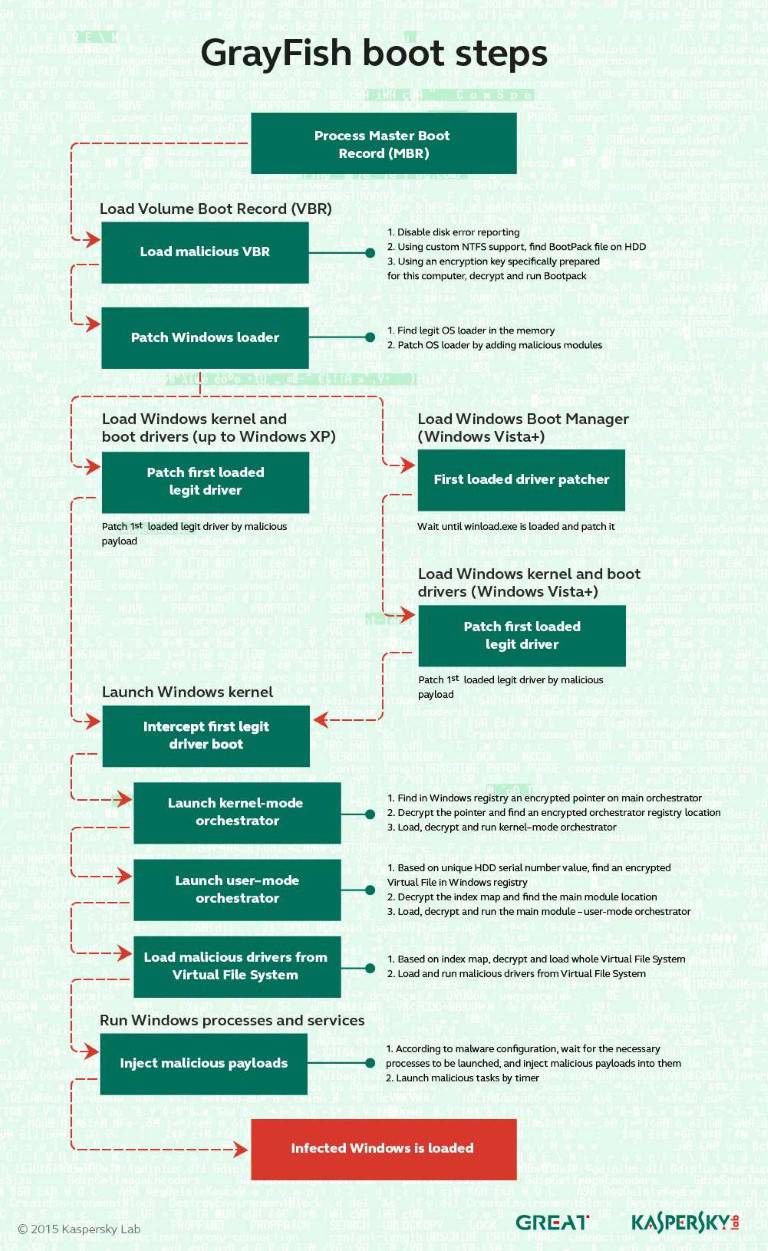
- GRAYFISH – The most sophisticated attack platform from the EQUATION Group. It resides completely in the registry, relying on a bootkit to gain execution at OS startup.
- FANNY – A computer worm created in 2008 and used to gather information about targets in the Middle East and Asia. Some victims appear to have been upgraded first to DoubleFantasy, and then to the EQUATIONDRUG system.
Fanny used exploits for two zero-day vulnerabilities which were later discovered with Stuxnet. - EQUATIONLASER – An early implant from the EQUATION group, used around2001-2004. Compatible with Windows 95/98, and created sometime between DOUBLEFANTASY and EQUATIONDRUG.
Kaspersky has included indicators of compromise for the malware strains it refers to and will publish an update in the coming days, it has said. ®