This article is more than 1 year old
GoPro cameras' WiFi security is GoAmateur
Slurp sick sports selfies without getting off your skateboard
Net nuisances can harvest the cleartext SSIDs and passwords of wireless networks accessed by sports selfie box GoPro.
The GoPro app collects and siphons wireless credentials so it can be used to log on to and manage cameras. Security researcher Ilya Chernyakov says the credentials which give access to the cameras could be mass harvested with a script to change a numerical token value within a generated URL.
"All you need to do, to access someone else’s Wi-Fi settings is to change this number," Chernyakov says.
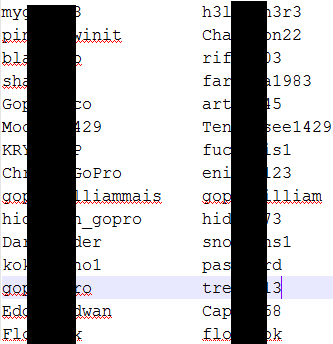
"I wrote a small python script that runs on a range of the URLs, extracts the settings from the response and puts them into a csv file.
"There were no complications, nor noticeable shape limiting for downloading so I was able to create a list of 1000 Wi-Fi names and passwords, including my own."
The attacks are limited since attackers can only access the sports cameras, but Chernyakov says scripts could be written to check nearby GoPro networks against harvested credentials.
The researcher disclosed the flaws to US CERT which nudged GoPro into fixing the flaws. Tests against a listed link failed, indicating the direct object reference vulnerability is closed.
"It takes time driving around snowboarders and divers, looking for Wi-Fi networks of the GoPro cameras," Chernyakov says.
He's too polite to say that the waterproof cameras could be used in other extreme - ahem - situations that could make the harvesting attack more dangerous to GoPro owners. ®
