This article is more than 1 year old
Google tells world where Apps users live after WHOIS SNAFU
Registration bug saw WHOIS privacy switch flicked to OFF after domain renewals
Names, home and email addresses, and phone numbers for a whopping 282,867 Google Apps domains have been exposed through previously borked private WHOIS records, Cisco boffins say.
The research is the work of Nick Biasini, Alex Chiu, Jaeson Schultz, Craig Williams and William McVey of Cisco's Talos team who today published an advisory detailing the impact of a "software defect" that slowly emerged in mid 2013 before reaching alarming levels when it was disclosed to Google last month.
They found admins are affected after they renewed their private WHOIS domain registration data.
The team probed 305,925 domains registered through registrar eNom and found that 94 percent were exposed prior to a fix being issue days after the private disclosure of the flaw.
"The reality of this WHOIS information leak is that it exposed the registration information of hundreds of thousands of registration records that had opted into privacy protection without their knowledge or consent to the entire internet," the team wrote.
"This information will be available permanently as a number of services keep WHOIS information archived.
"It’s possible to mine this information and leverage it for malicious purposes, such as spamming, spear phishing or other potential forms of harassment." Cisco's Talos points out that a "simple check" of privacy protection could have identified the problem.
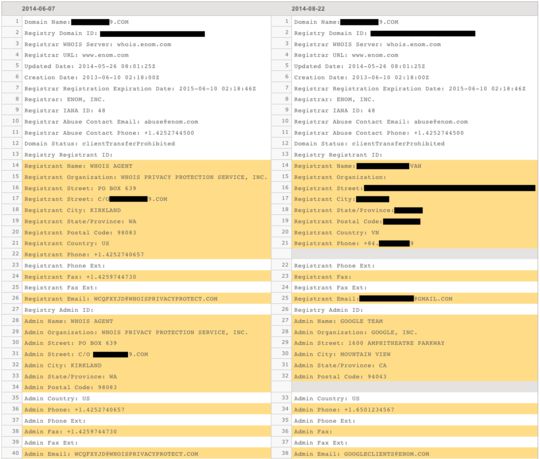
Privacy protected domains (l) are exposed after renewal (r)
Google overnight issued a letter to Apps admins apologising for the glitch.
"Dear Google Apps Administrator,We are writing to notify you of a software defect in Google Apps' domain registration system that affected your account. We are sorry that this defect occurred. We want to inform you of the incident and the remedial actions we have taken to resolve it.
When the unlisted registration option was selected, your domain registration information was not included in the WHOIS directory for the first year. However, due to a software defect in the Google Apps domain renewal system, eNom's unlisted registration service was not extended when your domain registration was renewed. As a result, upon renewal and from then on forward, your registration information was listed publicly in the WHOIS directory."
Cisco's team says affected administrators now risk having their operational security trashed since possibly real identities could be tied to their web assets.
They further point out the leaked information could result in more targeted phishing emails containing possibly legitimate name and contact details.
However, there is a silver lining; Some domains seemingly run by fraudsters have been caught in the kerfuffle having their probably fake WHOIS records exposed in what prove to be useful intelligence for threat attribution efforts.
Cisco's Talos points out that the affected domains are separate from those issued through Google Domains, and assets that have not faced a renewal period were not impacted. ®
