This article is more than 1 year old
POODLE vuln dogs Australian consumer modems
Freak out! Source tells Vulture South there's 100,000 vulnerable hosts out there
The persistent awfulness of consumer broadband modems is once again in evidence, with the Poodle and Freak bugs present in a huge number of Australian households.
The issue has hit Twitter, with some people reporting that ISPs are notifying them of possible malicious traffic – but without useful information on what to do.
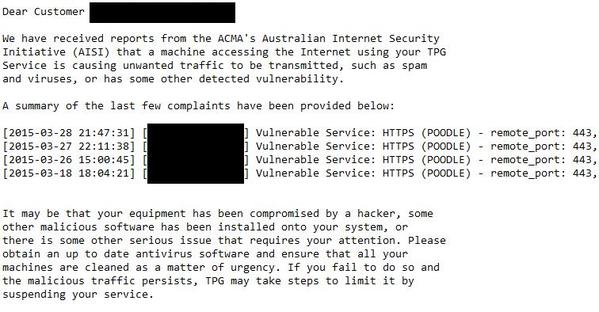
For example, the image above is a screen-grab that @OaaSvc posted, which identifies TPG as the service provider.
The Register has been told that the two bugs are still present in DLink, Netcomm and FritzBox devices (among, we're quite sure, many others), and that the security problems are exacerbated by devices that ship with external admin enabled by default.
There's no doubt that there are a great many vulnerable services still presented to the Internet in Australia. The Australian Communications and Media Authority's AISI Malware statistics page shows vulnerable services at more than 200,000 hosts and rising.
The “Other” chart on that page, first published on March 27, “includes” Freak and Poodle vulnerabilities, but The Register has reason to believe these two bugs represent nearly all of the “other” hosts.
Many of those hosts are un-patched servers – such as, for example, the Attorney-General's department (see Tweet below), but there could be as many as 100,000 Poodle/Freak vulnerable home devices as well.
I'll just leave this here shall I @acmadotgov? @CERTAustralia (see previous tweet) pic.twitter.com/mLbsbyMAYa
— Outrage as a Svc (@OaaSvc) March 31, 2015
It's also quite likely that a large number of turnkey VoIP services remain on the vulnerable list, according to The Register's source, who requested anonymity.
+Comment: It's almost impossible to expect home users en masse to learn even the most basic configuration tasks. There's no way Joe Sixpack is going to run a firmware upgrade and navigate a bunch of menus to find out where the remote management check-box is.
For that reason, it's also unfair to threaten blocking services to users who don't know what's going on.
It would seem at least prudent to Vulture South for ISPs to block traffic on the TCP ports used for remote management to vulnerable devices. ®
