This article is more than 1 year old
Google guru: Android doesn't have malware, it has Potentially Harmful Applications™ instead
And who installs five AV apps on their mobes?
RSA 2015 Malware doesn't exist on Android, Google says, but Potentially Harmful Applications™ do.
That linguistic flip is one of many at play in the Chocolate Factory's Android security division, which has dumped various general infosec terms overboard. Lead Android engineer Adrian Ludwig told the RSA Conference in San Francisco today that spyware is also a garbage term.
"There is so much structure and connotation around the word malware that internally we don't use that word; it just creates too much confusion … we have something like 20 different subcategories of [Potentially Harmful Applications™] things like trojans, fraud and abuse,” he said.
“I regret that we use the word spyware. When we say it, we mean that it grabs too much data and sends it off the device. There is a profound difference between grabbing all your SMS, and grabbing all your installed apps to send off your device. It's often called 'aggressive advertising'.”
The label churn is such that if Google found a spouse spying on another spouse, “we'd call it spouseware,” Ludwig said.
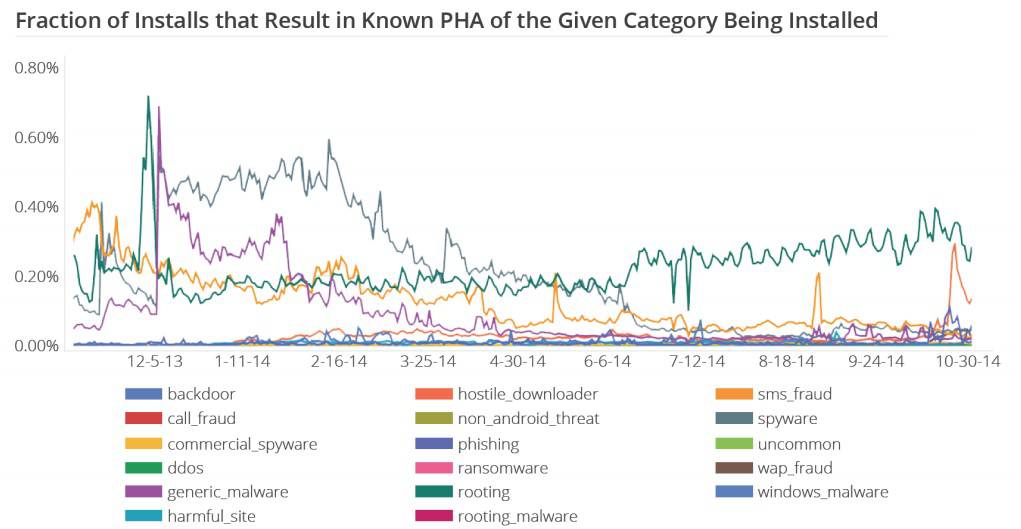
The dev has been flicking on data-monitoring switches in Android to determine the rate of vulnerability exploitation and exposure of data. So far, less than one per cent of devices have Potentially Harmful Applications™ installed, we're told, while exploitation is so slow as to be below the Chocolate Factory's visibility thresholds.
“That malware is increasing and most devices aren't protected is a myth,” he added.
It also seems to be a myth that rooted Android gadgets are dangerous to the enterprise. Ludwig did not recommend enterprises outright ban rooted devices, and said such modifications are probably not a problem for most organization's threat models.
He said that while impressive software security exploits surface often enough, their use in actual attacks is small: “I don't trust humanity any more than you do, but the scale of exploitation is small … in the meantime it feels like we may have a chance at wining the exploitation battle in mobile.”
In illustrating the low exploitation figures, he said of two "beautiful" exploits in wild, one was leveraged less than eight times per one million devices, and the other once per million, even though 99 and 82 percent of Android users, respectively, were at risk at the time of disclosure – and that's according to stats from Bluebox.
But that didn't stop users from freaking out. He says a whopping 40 per cent of users have antivirus installed, while a few security fanatics have five or more versions of the battery-sucking software installed.
The data crunching also revealed Europeans are more likely to be attacked via the POODLE downgrade SSL attack, while Asia is the least. Ludwig did not know why that difference exists, but says it is monitoring 400 million connections a day for the attacks. “If you're doing SSL downgrade, we're waiting for you.”
Ludwig's data is pulled from Chocolate Factory sources including Google Play stats, Safe-browsing for Chrome diagnostics, the Verify Apps feature, the Android Safety Net, and telemetry from Device Manager.
Ludwig's slides are available online [PDF] for all. ®