This article is more than 1 year old
Wrestling with Microsoft's Nano Server preview
The current technical glimpse is promising, but so painful
Microsoft has slipped out a preview of Nano Server, its ultra-slim deployment option for Windows Server 2016, along with the full preview versions of the forthcoming operating system.
Nano Server is “by far the most important change we have made in server since Windows NT", according to Microsoft Distinguished Engineer Jeffrey Snover, speaking at the Build conference last month, but the preview is low-key to say the least.
It is on the downloadable .iso image for Windows Server 2016 Technical Preview, but it is not a setup option. Instead, it sits in a separate NanoServer folder on the DVD and is delivered as a Windows Image file, NanoServer.wim.
The only documentation is here.
Installation is a matter of downloading and running a script to convert the image file to a .VHD (Virtual Hard Drive) that you can use with the Hyper-V hypervisor, which makes you wonder why Microsoft did not ship a .VHD in the first place.
That is just the beginning though. The image file, which is designed to slot into a Windows Server setup routine, cannot be booted as is. The next step is to use the right version of the DISM (Deployment Image Servicing and Management) tool to add packages to the image.
The getting started post does not make this clear, but it is best to add all the packages on offer, including the Guest package which installs the drivers for running on Hyper-V, perhaps with the exception of the one for failover clustering.
You also need to add an unattend script — Microsoft’s system for configuring Windows on first boot — in order to set a username and password for the server.
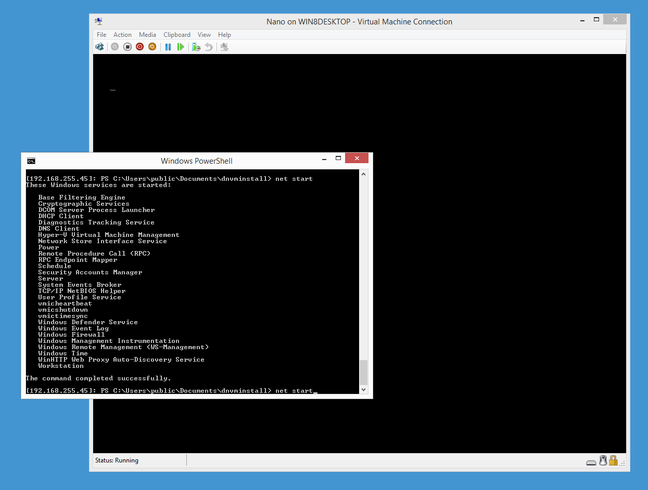
With these obstacles overcome, I booted Nano Server into a virtual machine (VM) with 1GB of RAM – more than enough. The first encounter with this new Windows variant is disorienting even for PC veterans, mainly because of the absence of a command prompt.
Windows Server Core, which includes command windows as well as enough GUI to run the likes of Notepad and Task Manager, suddenly seems like GUI luxury. Snover says such things are “client stack”, taking the view that all server administration should be remote; but it does add hassle getting started.
How then do you manage Nano Server? The help document makes several suggestions, including EMS (Emergency Management Services) via a serial connection (if you are lucky enough to have a serial port), remote access with PowerShell (Microsoft’s scripting and automation platform), WMIC (Windows Management Instrumentation Command-line), and WinRM (Windows Remote Management).
I tried three of these and was successful though with some frustrations. PowerShell remoting is the obvious choice, though only a subset of PowerShell cmdlets available.
The reason for the PowerShell limitations is another key characteristic of Nano Server: the fact that it does not run the .NET Framework (and there are no plans for it to do so).
It does run .NET, but only in its new-fangled CoreCLR guise, also known as .NET Core. This is cross-platform and open source, so it is not surprising that some Windows-specific things which PowerShell normally uses are not available.
When I wanted to see a list of Windows services, my first thought was to use Get-Service in a remote session, but it does not work; I had to use an alternative like Net Start instead.
At the Ignite event earlier this month Microsoft showed off a web-based management tool for Nano Server which includes Task Manager, Registry Editor, Event Viewer, Device Manager, Disk Manager, File Explorer and more, all hosted in the browser. That will help, but is not yet available, so bleeding edge previewers need to find other means.