This article is more than 1 year old
Android ransomware poses as FBI smut warning
Call the cops! Erm, actually don't
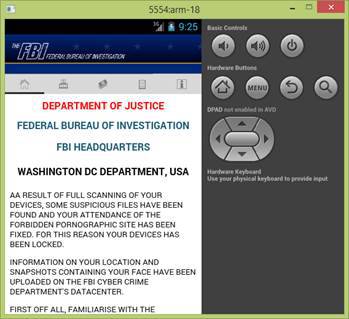
Cybercrooks have launched a new wave of Android ransomware that poses as a pretty convincing FBI-imposed porn-surfing warning.
Over 15,000 spam emails, including zipped files, have hit the inboxes of Android users in recent days, according to Romanian security software firm Bitdefender.
If activated, the ransomware demands $500 to restore access. Users that try to independently unlock their devices will see the amount increase to $1,500, with payment demanded via Money Pak and PayPal My Cash transfers.
The malware poses as an Adobe Flash Player update, a common malware slinging ruse.
“After pressing 'OK' to continue, users see an FBI warning and cannot escape by navigating away,” states Catalin Cosoi, Chief Security Strategist at Bitdefender.
“The device’s home screen delivers an alarming fake message from the FBI telling users they have broken the law by visiting pornographic websites. To make the message more compelling, hackers add screenshots of the so-called browsing history. The warning gets scarier as it claims to have screenshots of the victims’ faces and know their location," said Cosoi.
Android ransomware demands $500 to restore access
Bitdefender detects the threat as Android Trojan SLocker-DZ. This is one of the most prevalent Android ransomware families as the authors regularly create new variants.
The malware does not encrypt the contents of compromised smartphones, instead rendering the device’s home screen button and back functionalities inoperable.
"Turning the device on/off doesn’t help either, as the malware runs when the operating system boots,” according to Cosoi.
If ADB (Android Data Bridge) is enabled on the infected Android, users can uninstall the offending application. Users can attempt to start the terminal in Safe Boot.
This option loads a minimal Android configuration and prevents the malware from running, which can buy enough time to manually uninstall the malware. Although recovery may be possible prevention is obviously better than cure. ®
