This article is more than 1 year old
Boffins silently track train commuters without tripping Android checks
Smartmobe accelerometer data reveals your movements, isn't secured in any way
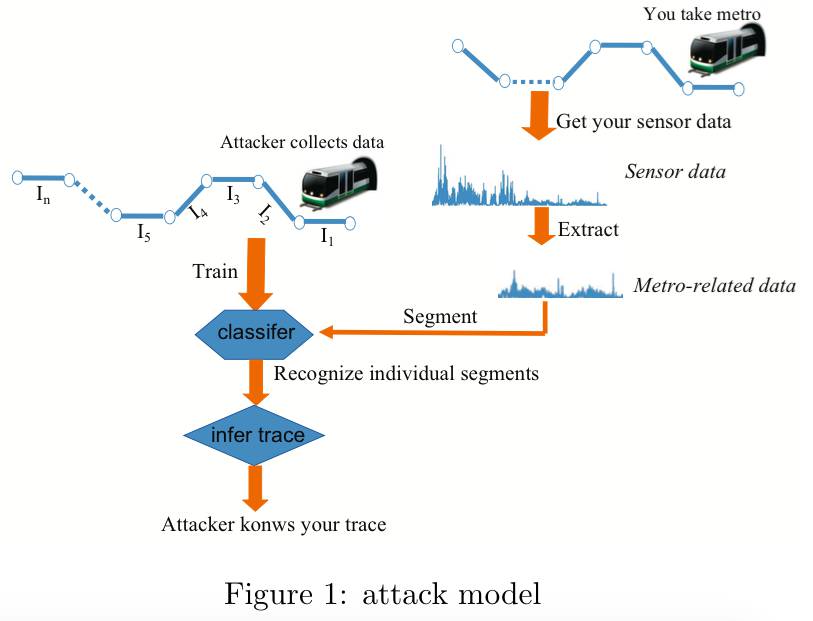
Nanjing University boffins Jingyu Hua, Zhenyu Shen, and Sheng Zhong have tracked commuter train trips with 92 percent accuracy using stolen phone accelerometer data.
The trio says tracking users on Android phones is possible in part because the platform does not require permission or consent to access the dataset. Here's the nub of their findings:
"We believe this finding is especially threatening for three reasons. First … it is extremely easy for attackers to create stealthy malware to eavesdrop on the accelerometer. Second, metro is the preferred transportation means for most people in major cities [which] means a malware based on this finding can affect a huge population. Last and the most importantly, metro-riding traces can be used to further infer a lot of other private information. For example, if an attacker can trace a smartphone user for a few days, he may be able to infer the user’s daily schedule and living and working areas, and thus seriously threaten her physical security."
The team says attacks based on their research could affect millions of people, and point to the 5.5 million who ride the New York City Subway each day, and the 6.4 million who travel on the Tokyo Metro daily.
In a paper describing their research, titled We Can Track You If You Take the Metro: Tracking Metro Riders Using Accelerometers on Smartphones (PDF) the boffins say they tested the attack on the local Nanjing Metro line and could identify up to 92 percent of targets travelling on the trains.
Accuracy increases with travel, peaking if a commuter travels across six stations.
The system uses an ensemble interval classifier compiled from semi-supervised machine learning techniques which crunches data from mixed 'obvious' accelerator sources, the team says in the paper.
That accelerator data is paired with train station location data to determine where a user is located.
"Simple" malware spread could be spread through established social engineering techniques, the team says. Given that Android won't ask for permission to access accelerometer data, such malware may stand a good chance to be accepted by Google.
The crew proposed defensive techniques including introducing noise into Android sensor data that would scramble location tracking. Applications that need clean accelerator data would need to trigger permission prompts.
Other defensive measures are less obvious, requiring battery consumption to be monitored.
It is far from the most privacy-risky attack to hit Android. Last week boffins found the factory reset function did not properly erase user files even allowing encryption keys to be recovered and subsequently brute forced. ®
