This article is more than 1 year old
VPNs are so insecure you might as well wear a KICK ME sign
Brit boffins' test of 14 prominent privacy tunnels finds leaks galore thanks to IPv6 mess
A team of five researchers from universities in London and Rome have identified that 14 of the top commercial virtual private networks in the world leak IP data.
Vasile C. Perta, Marco V. Barbera, and Alessandro Mei of Sapienza University of Rome, together with Gareth Tyson, and Hamed Haddadi of the Queen Mary University of London say vendor promises of user privacy and security are often lies that put users at risk.
"Despite being a known issue, our experimental study reveals that the majority of VPN services suffer from IPv6 traffic leakage," the authors wrote in the paper A Glance through the VPN Looking Glass: IPv6 Leakage and DNS Hijacking in Commercial VPN clients [PDF].
"Our findings confirm the criticality of the current situation: many of these [14] providers leak all, or a critical part of the user traffic in mildly adversarial environments.
"The reasons for these failings are diverse, not least the poorly defined, poorly explored nature of VPN usage, requirements and threat models."
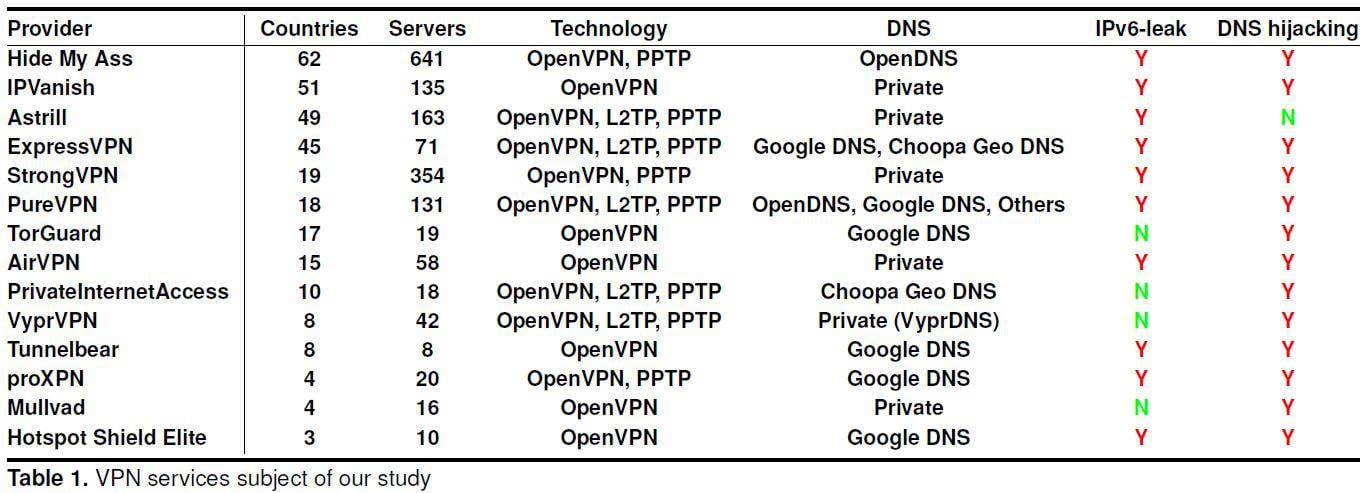
The team probed the top client software versions of providers including Hide My Ass, PrivateInternetAccess, and IPVanish. They established a campus dual stack OpenWrt IPv6 through IPv4 tunnel wifi network with updated Ubuntu, Windows, OSX, iOS 7, and Android clients. This simulated the environment where users would trust VPNs to protect them from a hostile network, they said.
All but provider Astrill were open to IPv6 DNS hijacking attacks and only four did not leak IPv6 data.
None were resistant to both threats. Here's how the authors summarise the situation:
"Whereas our work initially started as a general exploration, we soon discovered that a serious vulnerability, IPv6 traffic leakage, is pervasive across nearly all VPN services. In many cases, we measured the entirety of a client’s IPv6 traffic being leaked over the native interface. A further security screening revealed two DNS hijacking attacks that allow us to gain access to all of a victim’s traffic."
They found the most common VPN tunnelling technologies relied on outdated technologies like PPTP with MS-CHAPv2 which could be trivially broken with brute-force attacks.
The "vast majority" of commercial VPNs suffer from data leakage in dual stack IPv4 and IPv6 networks in a way the exposes "significant amounts" of traffic to public detection in contradiction to vendor claims.
"Most importantly we find that the small amount of IPv6 traffic leaking outside of the VPN tunnel has the potential to actually expose the whole user browsing history even on IPv4 only websites," they wrote in the paper. Here's the paper's explanation of the IPv6 mess:
"... whereas all VPN clients manipulate the IPv4 routing table, they tend to ignore the IPv6 routing table. No rules are added to redirect IPv6 traffic into the tunnel. This can result in all IPv6 traffic bypassing the VPN’s virtual interface. Although not a serious issue some years ago, increasing amounts of traffic is now IPv6, bringing the problem to criticality."
All of the DNS configurations used by the providers could be overcome by DNS hijacking attackers.
Recommended countermeasures included altering IPv6 routing tables to capture all traffic, and ensuring the DNS server can only be accessed through the tunnel. ®