This article is more than 1 year old
One MEEELLION users download Facebook-pwning droid game
Yeee-haarrrr! Cowboy Adventure rides off into sunset with saddles full of passwords
Threat researchers at security vendor ESET say a malicious Facebook-creds-stealing trojan masquerading as an Android game has been downloaded up to a million times.
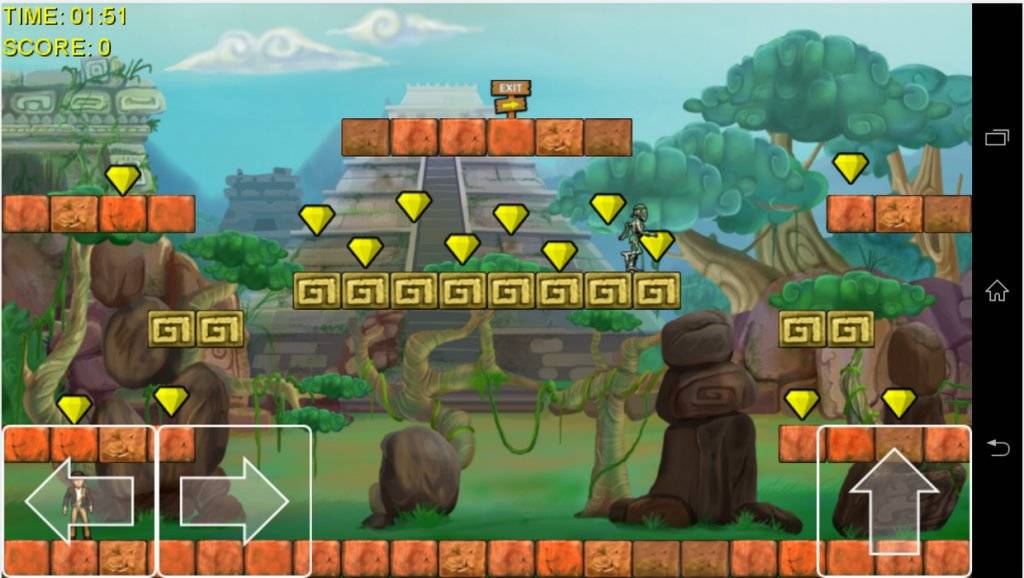
ESET chap Robert Lipovsky says the Cowboy Adventure game, and another also malicious game dubbed Jump Chess, has been since removed from Google's Play code bazaar after stealing an unknown number of Facebook credentials.
The VXers had created - or possibly stolen - a legitimate and seemingly popular game, lacing it with code that threw up a Facebook login screen as the app was used.
That cocktail meant that "... even though the number of potential victims may have been up to one million, there were many of them who were not tricked by the scam," Lipovsky says.
"Our analysis of these malicious games has shown that the applications were written in C# using the Mono Framework.
"The phishing code is located inside TinkerAccountLibrary.dll. The app communicates with its command and control server through HTTPS and the address to which to send the harvested credentials is loaded from the server dynamically."
Trustlook security boffin Tian Fang also reported the malware pointing out that the login scam attacked users outside of the US and Canada, and should have sounded alarms for users familiar with OAuth's signing requirements.
Fang says the scam spread to users in a victim's contact list, and likely used automated scripts to spread over social media.
The VXers were smart to use the Mono framework as it allowed them to evade analysis and set a location-based trigger to deactivate the malicious features and avoid antivirus detection. ®