This article is more than 1 year old
Next-gen secure email using internet's own DNS – your help needed
Use domain names to keep email contents safe from prying eyes. Except the NSA of course
A group of researchers from the US government and dot-com operator VeriSign are working on a new system for secure email: using domain names.
Highlighting the problems and security holes associated with current mail systems, the team from the National Institute of Standards and Technology (NIST), a subset of the US Department of Commerce, argues that by using a new set of security protocols built around the domain name system, it is possible to provide a much higher level of security in electronic messages.
Broadly, the idea is to allow for two types of email: signed and unsigned. Unsigned email would be secured using the current standard for secure email, Transport Layer Security (TLS).
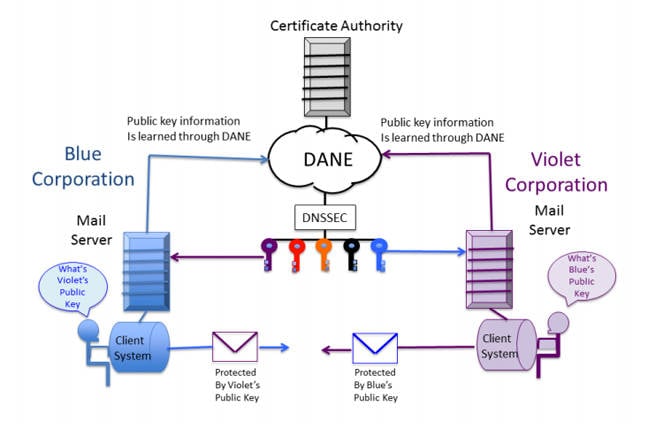
TLS would be used between email servers, then the new DANE security protocol (stands for "DNS-based Authentication of Named Entities") and the existing DNSSEC protocol would be used to protect the TLS keys.
The signed version would use the same system, but add in S/MIME on the end user's client device, again protected by DANE and DNSSEC. The related white paper [PDF] comes with a handy picture:
Although the paper argues that such an approach would provide a user-operated end-to-end security system rather than relying on your ISP's security, it does not envision an end-to-end encrypted approach where emails are encrypted and decrypted on your personal device.
In other words, those worried about NSA spying need not apply, since the encryption that is carried out will be done on servers that could be targeted without users' knowledge. It does note, however, that such a system could be used as a foundation for a full end-to-end encryption system.
There is also some concern that DANE could lead to governments accessing data, since it uses top-level domains as the security lynchpin and governments could exert control over a particular registry.
In many countries, governments either run or have close relationships with their "country code" top-level domain operators. And in the case of the now-hundreds of generic top-level domains, they fall under the purview of the United States government, given the contracts that each has signed with domain name overseer ICANN.
However, that concern has been described by one DNS expert as "more a sudden case of paranoia than the results of a relevant and reasonable analysis."
Market
The group does see a large potential use for business customers though. Not only would it increase the security and hence privacy of email, but it could also limit – or even kill off – spoofing of email and restrict the ability to send malware via email.
The biggest security hole in the proposed arrangement is of course the Certificate Authorities (CAs). Fake or invalid certificates are often used to gain access to server-based email systems, and the integrity of the system would rely on CAs providing the certificates that are then used to encrypt the information.
The researchers note that they would not see the use of self-signed certificates being allowed in such an approach. The fact that Verisign runs the world's largest registry operator no doubt makes the approach compelling.
But there are other barriers and potential problems.
By relying heavily on the DNS, it opens the approach up to the vagaries of that system, including split DNS resolution (so goodbye China), and the "limitations of DNSSEC as a trust model."
To work, mail systems worldwide would need to implement the approach. And they would have to only accept certificates using the X.509 protocol (something that is currently far from universal). Plus a large number of different companies' software products would need to be able to talk to one another.
But that's how it always is on the internet. Doesn't mean you shouldn't try.
The researchers are working on a proof of concept right now and are asking for fellow collaborators on a number of aspects, including: DNS resolvers (stub and recursive) for DNSSEC; authoritative DNS servers for DNSSEC signed zones; mail servers and mail security components; and extended validation and domain validation TLS certificates.
They are also taking public comments until 14 August and have set up a forum for discussion. ®
