This article is more than 1 year old
Imperva demos cloudy man-in-the-middle attack
Put down the club, you don't need to get a password
Dropbox, OneDrive, Google Drive, and Box can be raided via a man-in-the-middle attack, without an attacker needing access to users' plaintext credentials, according to security bods at Imperva.
Instead, in this paper [PDF] presented to BlackHat, the company's Application Defense Center says users' local sync folders serve just fine as data interception and exfiltration points. They also say work from BlueCoat suggests this formed part of an attack called "The Inception Framework."
The problem, the paper says, is that the OAuth 2.0 synchronisation token is exploitable. It's stored in a predictable location, and an attacker with access to the target's machine can perform a kind of pea-and-thimble trick to fool the victim's machine into handing over documents during the sync cycle.
The nub of the attack is this: "For each of the synchronization applications that we evaluated, by simply copying a token for an account into the right place in the end station, we were able to make the synchronization application switch to the account represented by the token. Therefore, an attacker can gain access to the victim's account by stealing a token and does not need to compromise the victim's password".
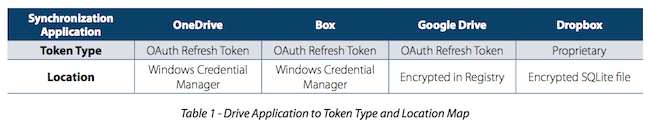
Where cloud sync tokens are stored Image: Imperva
The researchers built an application, Switcher, to carry out the attack, and they say that Switcher doesn't show any of the behaviours easily identified as malware. After an attack, it can be removed from the victim's machine.
So long as the user can be tricked into running Switcher (via phishing or a drive-by download): "This rather simple attack enables the attacker to share the victim's file synchronization account. The attacker is then able to access files that are synchronized by the victim and infect these files with malicious code", the paper states.
Here's the process described in the paper:
- 1. The attacker tricks the victim (using social engineering, for example) or uses an exploit in order to execute the Switcher. The Switcher then plants the attacker's synchronization token into the Drive Application.
- 2. When this first switch is complete, the Switcher copies the original synchronization token into the synced folder.
- 3. The Drive Application syncs with the attacker's account.
- 4. The attacker then has possession of the victim's synchronization token.
- 5. The attacker uses the stolen synchronization token to connect with the victim's file synchronization account (using, for example, the Switcher tool on the attacker's machine).
- 6. The Switcher tool runs for the second time on the victim's machine (hence, "double switch"), restoring the original synchronization token of the victim, essentially restoring the Drive Application to its original state.
Apart from exfiltrating data, Imperva explains the attacker could also modify documents (for example, to plant malicious macros in Word files, since that's become a thing again).
The attack can also be varied to give an attacker persistent access to a victim, since changes to a user's sync folder could trigger the Switcher processes. In essence, "the attacker uses the victim's cloud storage as a C&C and remote access infrastructure".
The researchers say the best way to deal with the attack is for users to deploy Cloud Access Security Brokers to monitor enterprise cloud service usage and behaviour, and to wrap their enterprise data in solutions that identify "abusive access". ®
