This article is more than 1 year old
SONY HACK WAS WAR says FBI, and 'we're still struggling to hire talent'
Cybercrims may be safe at home, but Feds dare them to go on holiday
Cloudsec Yesteryear's hack of Sony Pictures was an act of war, stated FBI Supervisory Special Agent Timothy Wallach, who delivered the FBI's gradation system of cybercriminals to net security conference Cloudsec on Thursday, 17 September.
US agencies have fingered the North Korean government for the Sony attack repeatedly, initially to much scorn as the nation is popularly believed to be residing in the technical dark ages.
However, the Norks role in the breach has been increasingly accepted, as information about the NSA's role in attribution has been made public.
Presenting the act of war at one end of the spectrum, with hacktivists at the other end, FBI Supervisory Special Agent Timothy Wallach told Cloudsec about the agency's ongoing efforts to deal with cybercrime.
Wallach made it clear the FBI distinguished hacktivists – a term he suggested covered ideological actors, including everyone from LOIC and Lizard Stresser ego-hackers, through to those defacing police websites following the shootings of young African American men – from those cybercriminals who were motivated by financial gain or espionage.
The hack of Sony pictures, he suggested, was an act of warfare, though it remains unclear how it might be considered a military act of sabotage, other than its nation-state backing.
Who's doing the hacking? @FBICyberCrime #cloudseclondon pic.twitter.com/Zj8HeqTfbv
— Paola Wright (@paolaw27) September 17, 2015
According to Wallach, who is currently assigned to lead the Cyber Task Force in the Seattle Field Office of the FBI, reports of breaches increased by 55 per cent between 2013 and 2014.
These breaches often targeted personal identifiable information, although an increasing number went after healthcare information, which Wallach regards as a larger target.
Intellectual property espionage from China remains an issue, especially from the People's Liberation Army (PLA) advanced persistent threat Unit 61398, which was exposed by Mandiant in 2013. Unit 61398 had been known by the codename "Byzantine Candor" by US intelligence agencies since 2002.
The five-man strong PLA hacking team is unlikely to face attention while residing in China, Wallach stated, although they would be picked up were they to travel outside of the country.
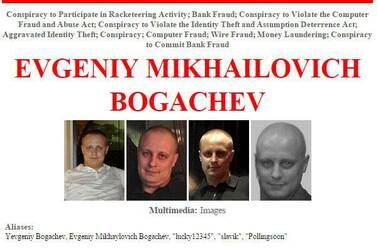
$3m bounty for capture. Also known as "Slavik" and "lucky12345".
Also mentioned was one Evgeniy Mikhailovich Bogachev, also known as Slavik and Lucky12345. The creator of the GameOver Zeus trojan has a $3m bounty on his capture, which Wallach encouraged attendees to have a think about.
A criminal complaint (PDF) filed in the District Court of Nebraska states that Bogachev "has been a member of a long-running conspiracy to employ widespread computer intrusions, malicious software, and fraud to steal millions of dollars from numerous bank accounts in the United States and elsewhere".
Research delivered at Blackhat earlier this year, and produced by a coalition of Fox IT, Crowdstrike, and the FBI, suggested that Bogachev "had obtained a level of protection [from the Russian security agencies], and was able to get away with certain crimes as long as they were not committed against Russia".
In his book Spam Nation, Brian Krebs offered details about the criminal conspiracy, called the Russian Business Network, which Bogachev is alleged to be a member of. Krebs' focus is on spammers who enjoyed FSB protection via donations made to a volleyball league.
The spammers' bread-and-butter was in attracting people to purchase drugs through unlicensed online pharmacies, which were sold at much lower prices than they retailed for in the US. This may offer an explanation as to why healthcare information is becoming such a large target for hackers, although this was not suggested by Wallach.
