This article is more than 1 year old
The last post: Building your own mail server, Part 3
Adding some much-needed spam and virus filtering
Setting up ClamAV
The ClamAV package is installed with Amavis on OpenBSD, and includes a daemon that can run in the background, checking content that's passed to it by other applications, including Amavis. Before you start it, however, two config files need to be updated. The first is /etc/clamd.conf, where you need to comment (ie, put a # at the beginning) the line that says 'Example' and then uncomment the following entries:
LogSyslog yes LogFacility LOG_MAIL LocalSocket /tmp/clamd.socket User _clamav AllowSupplementaryGroups yes
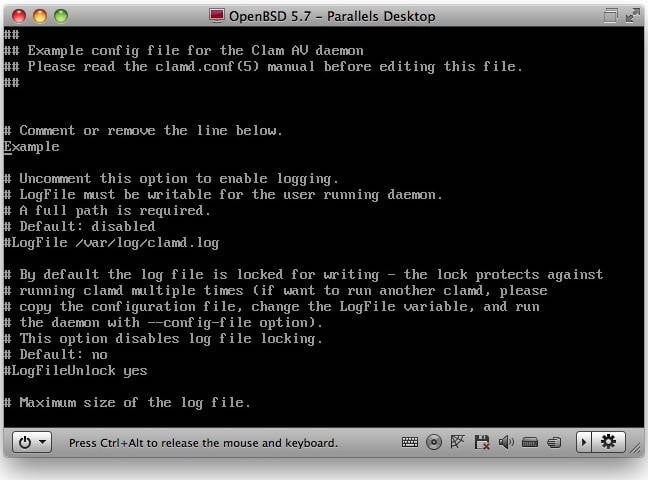
ClamAV won't work at all until you edit its config file
The second file is /etc/freshclam.conf, which controls the process that periodically updates the virus definitions. Again, comment out the Example line near the top, and remove the # at the start of the lines.
LogSyslog yes LogFacility LOG_MAIL
You'll also need to add the clamav user to the /etc/group file, adding it to the vscan group. Find the line at near bottom that starts _vscan:*:530: and edit it so that it reads.
_vscan:*:530:_clamav
Now, both freshclam and clamd can be started with their scripts /etc/rc.d/freshclam and /etc/rc.d/clamd respectively. You should see startup messages in /var/log/maillog. Don't panic if you see a warning about your ClamAV version; it will still be detecting viruses.
Configuring Amavis
Amavis is configured by editing the file /etc/amavisd.conf. This looks rather different to many of the config files we've seen before, and is, frankly, a bit on the scary side; it's actually a Perl script. We'll start with some straightforward edits. First, near the top, you'll see a line that says
$max_servers = 2 ;
which you should change to a higher number, say 7 to start with. This is the number of scanners Amavisd will have ready for incoming connections. Next change the mydomain setting, for example
$mydomain = 'nigelwhitfield.com' ;
A little further down, you can add info about other domains, such as virtual domains, to the local_domains_maps line; this starts with an @ as it's an array of variables. To match our config so far, you'd update it to read:
@local_domains_maps = ( [“.$mydomain”,“fancynewdomain.com”]) ;
Make sure you don't mess up the punctuation; Perl can be very particular. You should also add details of your network to the @mynetworks line; note that a comma isn't used between entries there. Scroll down and you'll find a series of entries starting with $virus_admin which specify the user name that will send various alerts; you can either change there, or create a 'virusalert@yourdomain' alias in Postfix.
Next, find the entry for $forward_method, and uncomment it, so it reads
$forward_method = 'smtp:[127.0.0.1]:10025' ;
This tells Amavis to pass mail back to Postfix on port 10025. An entry near the top called $inet_socket_port is uncommented by default and tells it to listen on port 10024.
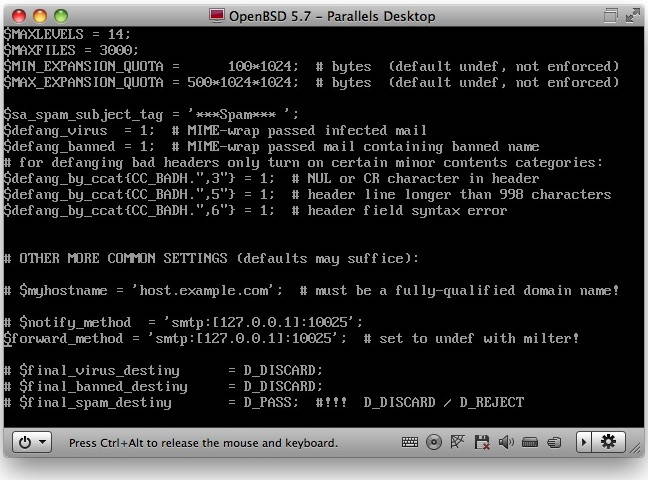
The Amavis config file is complex - edit with care!
Work through the file — you don't need to change much else for now — and you'll see options for banned file extensions; some of these will have a comment (#) at the start of the line, and the active ones won't. You may want to change these later, depending on which type of files you want to accept via email. Carry on scrolling down until you find the AV scanner definitions. One of these is for ClamAV, and starts
#['ClamAV-clamd',
Remove the comments on that line, and the following three, and also make sure the name of the socket in the second line matches the one in clamd.conf. You should end up with something that looks like this:
# ### http://www.clamav.net/
['ClamAV-clamd',
\&ask_daemon, ["CONTSCAN {}\n", "/tmp/clamd.socket"],
qr/\bOK$/m, qr/\bFOUND$/m,
qr/^.*?: (?!Infected Archive)(.*) FOUND$/m ],
# #
That's all for now, though there's a lot more you can tweak in Amavis, including error messages, the level at which messages are marked as spam, and optionally rejected, and so on. The Amavisd site has lots more detail. For now, though, start Amavis running with
/etc/rc.d/amavisd start
If all is well you should see entries in the maillog showing the startup, and confirming that various unarchiving tools have been detected along with the ClamAV scanner.
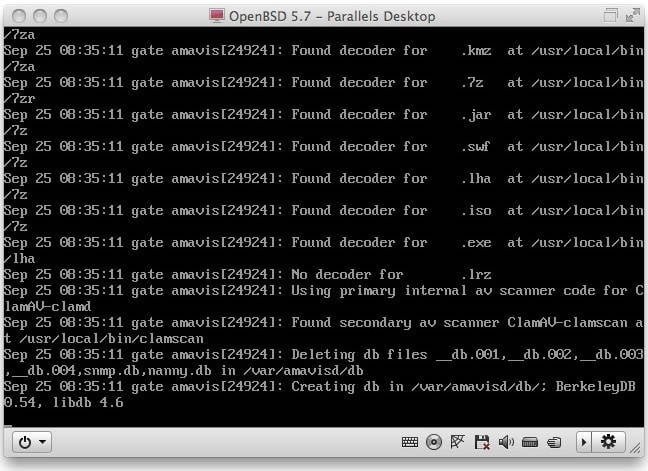
Check the log file after starting Amavis, and it should have detected ClamAV
