This article is more than 1 year old
How to evade Apple's anti-malware Gatekeeper in OS X and really ruin a fanboy's week
Need a better latch on that gate
The myth that Macs are inherently more secure than Windows PCs has taken another hit.
Patrick Wardle, a former NSA staffer who now heads up research at crowdsourced security intelligence firm Synack, has found a new route around Apple's defensive Gatekeeper technology.
Apple's Gatekeeper utility is built into OS X, and is designed to verify the integrity and origin of software installed on Macs. By default, only code digitally signed by registered developers – or, with more restrictive settings, only packages from the Mac App Store – should be allowed to run. The technology was introduced in July 2012.
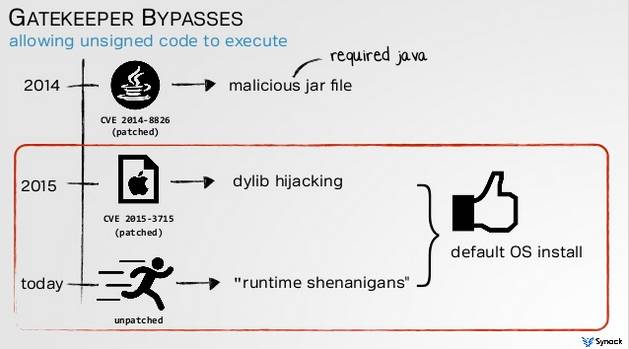
Wardle has found a way around these restrictions. During a presentation at the Virus Bulletin conference in Prague on Thursday, Wardle detailed unpatched vulnerabilities he has found in Gatekeeper that allow attackers to spread unsigned binaries containing malware, circumventing Gatekeeper in the process.
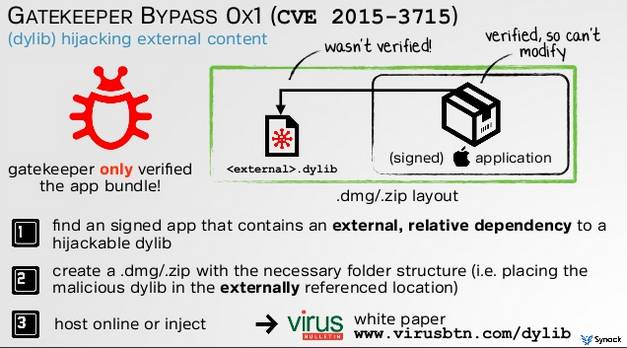
The essential problem is that Gatekeeper only verifies the signatures on app bundles. Malicious unsigned binaries stored outside an app can still be loaded without Gatekeeper interfering.
In other words, when a legit signed application is run, and it pulls in an outside library file, if an attacker can replace that file with something malicious, OS X will load that file into the app and allow it to execute, no questions asked – even if the external library is unsigned and completely untrusted.
It's therefore possible to inject dodgy code into an otherwise normal application – a stepping stone to infecting a Mac.
Of course, if you can modify that external library, you may be in a position to cause damage to the Mac, or snoop on the user, without any help from Gatekeeper – but that doesn't change the fact that Wardle has uncovered a design flaw in Apple's system.
"External content is not verified by Gatekeeper" at run-time, and this remains a vulnerability months after Apple patched a related dylib hijack vulnerability, Wardle told El Reg.
Gatekeeper still permits run-time shenanigans
This latest Gatekeeper bypass follows previous research from Wardle that showed it was possible to sidestep Apple's Gatekeeper using a malicious dylib (equivalent to a DLL on Windows).
Aside from this, dodgy software can always exploit other vulnerabilities to evade Gatekeeper entirely, as was the case for the infamous Flashback malware.
Wardle has presented at numerous security conferences over recent years about the various security shortcomings of Mac OS X in general, as previously reported.
Gatekeeper ... and some of the ways around it
On Wednesday, Apple released OS X "El Capitan," its latest desktop operating system, but it too is vulnerable. Wardle has notified Apple about his latest research and a fix is likely. In the meantime, users should stick to downloading software from the Mac App Store, Wardle suggested. As things stand, Gatekeeper by itself only protects Mac fans from lame attackers, according to Wardle.
While Apple's Gatekeeper provides for basic code-signing validation, it is essentially a blacklisting technology that many developers have legitimate reasons for disabling. Wardle's research is nonetheless noteworthy, especially since Macs are becoming an increasingly common desktop option in companies, partly as a result of the industry-wide BYOD trend.
"Anyone who has read Patrick [Wardle]'s research will realize that many of the security mechanisms built into OS X are not suitable for enterprise-level security," said Andrew Avanessian, VP at security tools firm Avecto.
"With Gatekeeper being simply bypassed, it is time for organizations to consider layering extra defenses on top – such as privilege management and application control – in order to mitigate attacks and prevent unwanted content from executing."
As Mac adoption in the enterprise increases, so too does the frequency of attacks, and this calls for a fresh approach to security for the platform, according to Avanessian.
"Whilst Macs have come a long way in the past 20 years, the security offerings have stood still – even the major vendors offer little more than basic antivirus," he added. "It is time for enterprises to think differently when it comes to Macs and learn the lessons from Windows." ®
