This article is more than 1 year old
Avast antivirus hole patched after public Project Zero slap
Man-in-the-middle diddle leads to remote execution fiddle
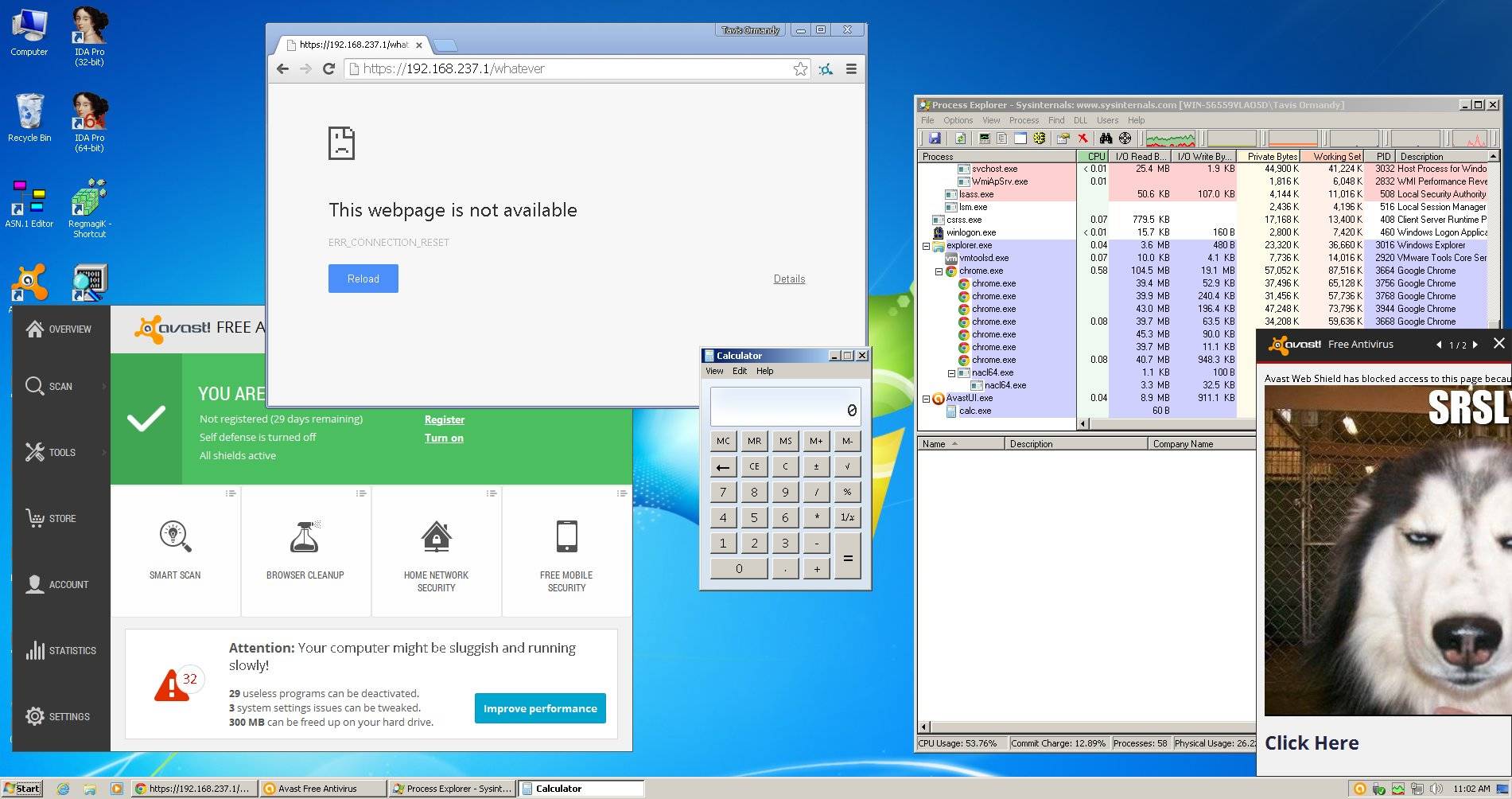
Google Project Zero hacker Tavis Ormandy has found a since-patched vulnerability in Avast antivirus that allows attackers to gain remote code execution privileges.
Ormandy says the man-in-the-middle diddle Avast uses to conduct encrypted traffic analysis as it hits browsers is insecure, thanks to bad X.509 certificate parsing.
It appears Avast users would need to follow a link generated by attackers and possibly ignore any code execution warnings in order to be p0wned.
"If you're gonna MITM Chrome's SSL at least get an intern to skim your X.509 parsing before shipping it," Ormandy says.
The hacker noted the vendor's seven day patch turn around time but chided one Avast security bod, saying in a tweet that the vendor is lucky attackers have not built worms targeting its products.
@Jindroush You say "layered defense", I say "attack surface". It's a miracle you haven't been wormed, sandbox your code urgently.
— Tavis Ormandy (@taviso) September 28, 2015
Ormandy released proof of concept information on the Google Project Zero asset.
Avast has not yet updated its site detailing the patch release notes. ®