This article is more than 1 year old
BitLocker popper uses Windows authentication to attack itself
Microsoft squashes offline logic flaw that makes lost laptops dynamite
Blackhat Europe Synopsys security boffin Ian Haken says un-patched PCs in enterprises are at risk of having user accounts popped and Bitlocker bypassed, in an attack he describes as "trivial" to perform.
The attack vector, sealed off in the latest round of Redmond patches (MS15-122), affect those Windows machines that are part of network domains, notably those in enterprise fleets.
Only sadistic sysadmins whose users suffer having to enter pre-boot passwords are immune, Haken says.
Haken says attackers with access to a lost or stolen laptop can spoofing the relevant network domain, to set up a fake user account which matches the username for the victim's computer.
The fake account needs to be set with a creation date in the past. The password set does not matter.
Once the victim machine connects to the spoofed domain, Windows will throw a password reset prompt that will change the credentials in the computer's local cache.
The laptop could then be disconnected from the spoofed domain and accessed using the changed credentials.
Haken says in the paper Bypassing Local Windows Authentication to Defeat Full Disk [pdf] presented at BlackHat Europe the attack is not foiled by Redmond's Trusted Platform Module. Here's a sample of his thinking:
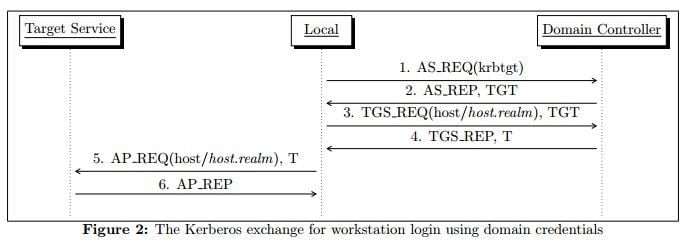
... the domain controller is remote, and since the attacker has physical control of the machine, the attacker also has control of network communication and can direct communication to an attacker-controlled mock domain controller.Since a machine with passwordless BitLocker will transparently retrieve the decryption key and boot to the Windows login screen, Windows authentication becomes the attack surface for defeating BitLocker.
There is no easy fix without Microsoft's patch. Those admins who do not or cannot apply the patches can disable local credential caching, but that means users cannot login offline. ®