This article is more than 1 year old
Mixing ERP and production systems: Oil industry at risk, say infosec bods
There will be pwnage
Black Hat Europe Hackers might be able to bridge the gap between supposedly air-gapped systems in oil and gas production by pivoting from enterprise planning onto production systems.
Vulnerabilities and insecure installations in SAP business software and other enterprise systems might be used to interfere with loosely-couple but nonetheless connected industrial control systems, security researchers from ERPScan warn.
Alexander Polyakov and Mathieu Geli outlined the risk during a presentation at last week’s Black Hat Europe conference in Amsterdam. As a worse case scenario, insecure setups might be exploited to interfere with operational processes and lead to disruptions in production or even sabotage.
High profile cyber attacks on the oil and gas industry against Saudi Aramco and RasGas involved the use of wiper-style malware to trash corporate computers.
Production was unaffected even though PC systems used for sales and accounts were rendered unusable.
Yet the little-publicised security risks highlighted by Polyakov and Geli had no part to play in either of those attacks, the two researchers told El Reg. Instead, the risks are more comparable to the way the Target hackers used a HVAC management system to infiltrate a corporate network before planting malware on point of sale terminals.
SAP bugs and SCADA exploits
Polyakov and Geli’s research focused on SAP and Oracle systems are widely used in oil and gas industries. There are even specific SAP modules for oil and gas such as SAP Upstream Operations Management (UOM) or SAP PRA (Production and Revenue Accounting), Oracle Field Service, and Oracle Enterprise Asset Management.
An estimated 75 per cent of oil production (70 million barrels a day) is controlled by SAP systems.
Mission-critical business applications are often connected between each other using different types of integration technologies. Enterprise applications which are located in the corporate network are usually connected with devices in industrial control systems.
Plant devices that collect data about oil volumes, for example, interface with corporate resource systems.
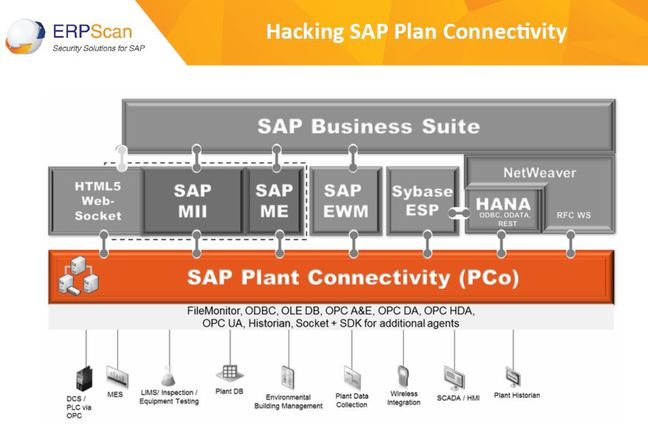
Explanation: Here's a plan of how miscreants could hack into an SAP network
“That’s why even if you have a firewall between IT and OT [Operations Technology] there are some applications which are connected,” a whitepaper put together by the two researchers explains. “That is why it’s possible to conduct such attack and pivot from IT network (or even the net) into OT network, up to field devices and smart meters.”
At worst the risk exists that hackers might be able to gain access to upstream oil and gas exploration facilities, mid stream transport and processing plants, and downstream refineries and sales operations.
Within the upstream the ERPScan researchers said that attackers could cause mayhem with burner management system by controlling the ratio of flammable mixtures. The simplest attack here is to turn off purge functions, but other attacks against industrial control systems create even more serious risks not excluding sabotage or the shutdown of refineries, the ERPScan duo warned.
SAP’s xMII (Manufacturing, Integration and Intelligence) system, SAP Plant Connectivity, SAP HANA Database, SAP Oil and Gas extension for ERP, and other enterprise resource planning apps were studied by the two researchers.
Problems arise because enterprise management systems and industrial control systems, although theoretically air-gapped, are often linked in practice so that management can easily get real-time info on what’s happening in plants, among other reasons.
SAP xMII systems collect process data, feeding it to OPC [OLE for Process Control] servers that manage programmable logic controllers and other industrial control devices. ERPScan discovered a now resolved SQL injection security flaw in the J2EE engine of SAP xMII. It might be able to hack the internet-facing SAP portal to gain access to SAP xMII systems.
Separately, ERPScan discovered a memory corruption and execution vulnerability in the SAP HANA database.
ERPScan has become well known as a specialist in security research in ERP systems, not infrequently turning up flaws in systems from SAP and Oracle.
Misconfigurations in systems represent an even bigger risk than software flaws for oil and gas firms. As well as hard-coded passwords there are examples of ERP systems and industrial control systems running on the same physical box, according to ERPScan.
“We have SAP system such as SAP ERP, which is located in IT network and is connected to SAP xMII,” Polyakov, ERPScan chief technology officer, told El Reg.
“From this Windows server an attacker can send commands to PLC devices which are usually insecure. For example, by using the modbus protocol without authentication. So, a hacker would only need to hack SAP PCo [SAP Plant Connectivity] server to be inside OT [Operations Technology] network. He can do this by hacking SAP xMII and extracting users and passwords from the PCo,” he added.
SAP Plant Connectivity acts as a hub and a link between industrial data to the business applications, according to ERPScan.
“It's a practical observation that often both SAP PCo + OPC [OLE for Process Control] servers sit on the same hardware,” Geli, a security engineer, added. “To have a working setup where PCo sits on a box and speaks to an OPC server on another is tedious, and often people circumvent that problem by setting up both on the same, having probably the (bad) feeling that it's not that critical because the machine is on the OT side.”
The oil and gas sectors are also threatened by frauds involving the theft of resources during upstream or downstream processes, the researchers warn.
