This article is more than 1 year old
Video malvertising campaign lasted 12 hours? Try two months
Vid crapware issue worse than you thought - researchers
A malvertising campaign exploiting online videos to fling poison at netizens actually lasted for two months rather than the 12 hours previously reported, according to new research which suggested the previously unfavoured medium may be ripe for exploitation.
Contrary to The Media Trust's report that a video malvertising campaign hit "some of the largest, most heavily trafficked sites for more than 12 hours", an investigation by malvertising monitors ClarityAd discovered it had actually been ongoing for two months.
Two security experts who have analysed the vector extensively stated that the duration of the mischief suggested the industry needed to put much more effort into dealing with the new threat of video advertising malware.
ClarityAd's CTO and co-founder, Jerome Dang, as well as Malwarebytes' senior security researcher, Jérôme Segura, stated that "the main bad actor" in the two-month campaign was the domain BrtMedia.net, in their in-depth analysis of the miscreant's methods.
To date malvertising has mostly targeted "display" advertisements, whether they be based on patch-addicted Flash or images with some nasties embedded.
The use of video advertisements has been a less exploited medium due to the relative security of the video advertising XML compared to the horror of Javascript, and the much higher cost of running a video campaign.
That there is, as ad firms claim, so little unsold advertising inventory in the video advertising world additionally means that the sales environment is handled far more manually. This is in stark contrast to the ecology of display advertisements, where the business need to monetise has weakened the controls which may be expected to prevent less-committed malicious actors from succeeding.
However video's XML - VAST (Video Ad Serving Template) proved insufficient for advertisers, who demanded an extension to execute code in advertisements. That led to VPAID (Video Player Ad-Serving Interface Definition), a specification released by the Interactive Advertising Bureau. It was this which made video malvertising campaigns feasible.
Route of all evil
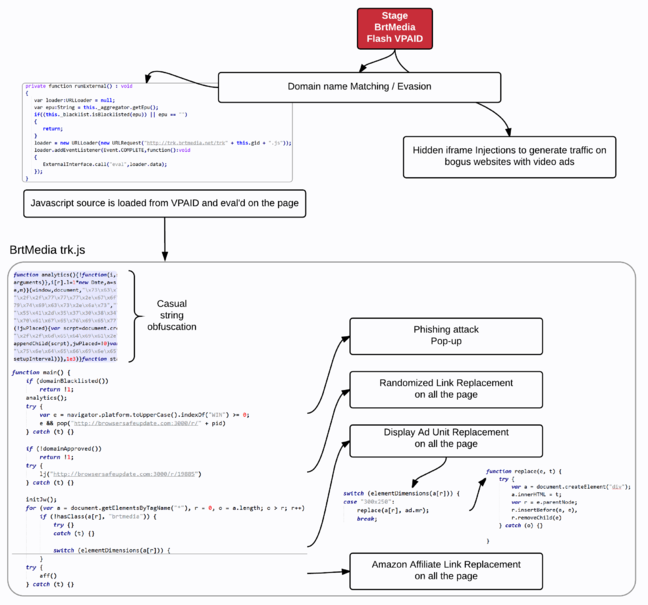
Businesses' vulnerability to protecting their revenue seemingly demands the frequent obfuscation of VPAID Flash files, "maybe in the hope of protecting some trade secret", suggested the researchers. In doing so they "completely ruined the security model originally thought out with VAST."
Subsequently, the advertising ecology from Real Time Bidding (RTB) which has allowed a torrent of poison in display ads, was exported to the video advertising market.
Programmatic advertisements now account for 39 per cent of that market according to a recent study by eMarketer.
The result is that: "Publishers now have no idea who serves what ads on their websites, making it virtually impossible to police for compliance and security – unless they rely on dedicated audit and scanning technology."
BrtMedia's campaign ran as a VPAID video advertisement on Facebook's LiveRail "Monetization Platform for Publishes" since early September, and was most recently seen in early November. LiveRail's RTB exchange locates bidding on the client-side, meaning that regardless of the result of the auction the malicious domain will be present in browser logs.
If the bid is indeed won, "the website's video player parses the ad's XML and executes the VPAID code (bidder.swf)."
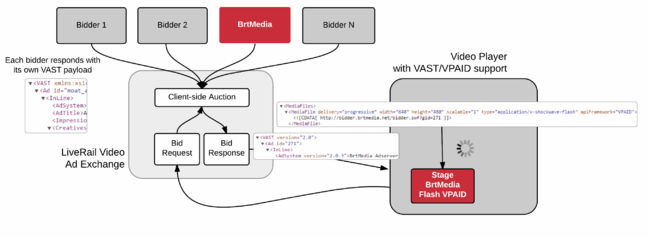
Dodging iframes, VPAID allows attackers direct access to the DOM - where BrtMedia's Javascript performs four naughty tricks, as the researchers explained:
- First it attempts to open a pop-up window to a fake Flash update URL at browsersafeupdate[dot]com. It also loops through each link on the page, and for each of them it assesses a 1 per cent chance of replacing it with the same malicious URL. From a visitor’s perspective, it looks as if the website itself is sending you to a malicious page!
- Secondly, the Javascript also loops through all ad formats on the page and replaces them with its own ads (amazon affiliation links).
- Thirdly, when the ad format is 300×250, it instead bootstraps a whole video player, looping through video ads on the same ad platform that it used to get to the page in the first place.
- Finally, BrtMedia also injects whole bogus websites on the page (i.e. turkey sandwich recipes), to profit from fake video ads traffic. This is done via a hidden iframe at http://trk.brtmedia.net/r/.
The Register has attempted to contact LiveRail regarding the platform's use in this campaign but has not received a response at the time of publication. ®
