This article is more than 1 year old
Bounty hunters won't blink until you dangle US$1500 bug reward
And to get the good ones working for you, you'll need ten times that sum
Organisations that aspire to operate bug bounty programs should be prepared to pay at least $1500 for impactful vulnerability reports, according to Bug Crowd.
A document and questionnaire published today by the managed bug bounty platform offers businesses the ability to pair their current security postures, revenue, and staff with a recommended payout list for bugs.
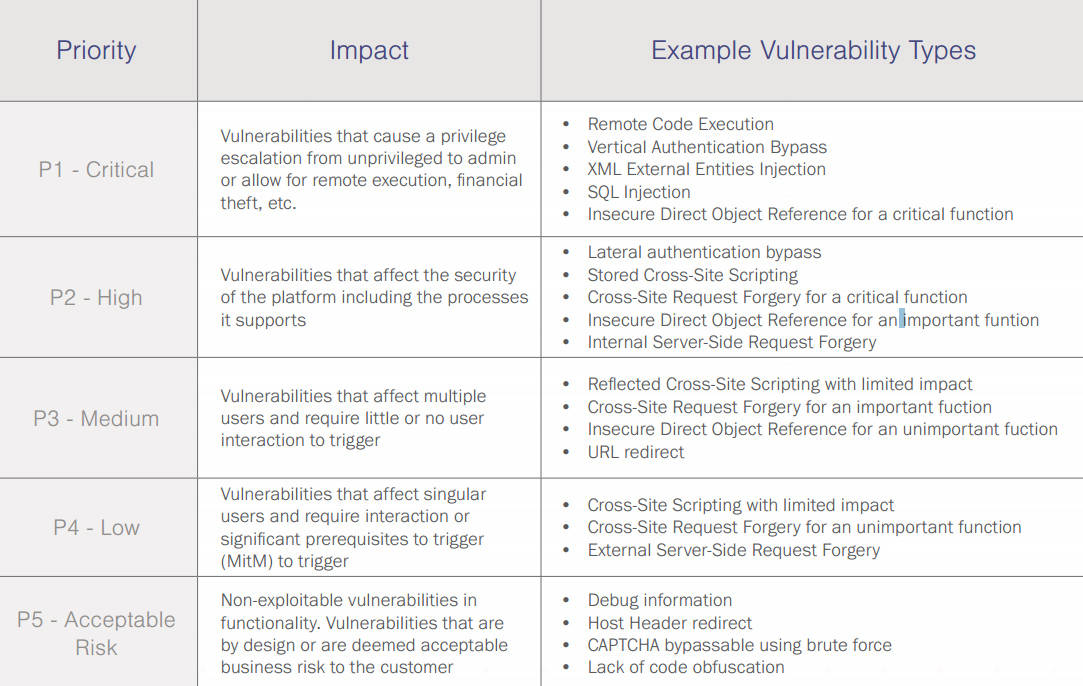
Critical or P1 bugs are worth anywhere between US$1500 to $15,000 depending on the security maturity of an organisation.
The lowest but not lamest bugs are worth at least $100 to $300.
This reporter tested the security deprived limits of the multiple choice questionnaire and nowhere was a t-shirt bounty offered as an acceptable payment (although many researchers willing to report holes freely in the name of better security say they are okay with cheap rewards).
BugCrowd boss Casey Ellis says the receives lots of inquiries about appropriate rewards.
"These are great questions, and frankly, the answers to them will continue to evolve as the market for bug bounties matures," Ellis says in the company's report (PDF).
"While the market continues to evolve, the key to success remains the same; to run a successful bounty program you must attract the right researchers with the appropriate incentive.
Bug Crowd's questionnaire.
As with any marketplace the ultimate proof of value is in the transactions themselves, and this market is at the very beginning of getting started."
An organisation with basic security is one that regards infosec as a "necessary evil" with a chief information security officer in charge of a small and minimally-skilled security team that is "subservient to IT".
Advanced organisations have their chief information security officer reporting to the CEO and chatting to the board. In these elusive organisations security is documented and formal, and "part of the culture".
It is okay to be a cheap-skate, however. Large organisations can hand out things like frequent flier points instead of money, but should eventually switch over to doling out paper.
Organisations considering bug bounties or bug disclosure without reward should foremost set up a dedicated and easy-to-locate email address through which bugs can be submitted.
Correspondence is king as vulnerabilities that are ignored have a high chance of being dropped as zero day in places like the Full Disclosure mailing list. ®