This article is more than 1 year old
$17 smartwatch sends something to random Chinese IP address
Samsung Gear 2 also has some problems, researcher says
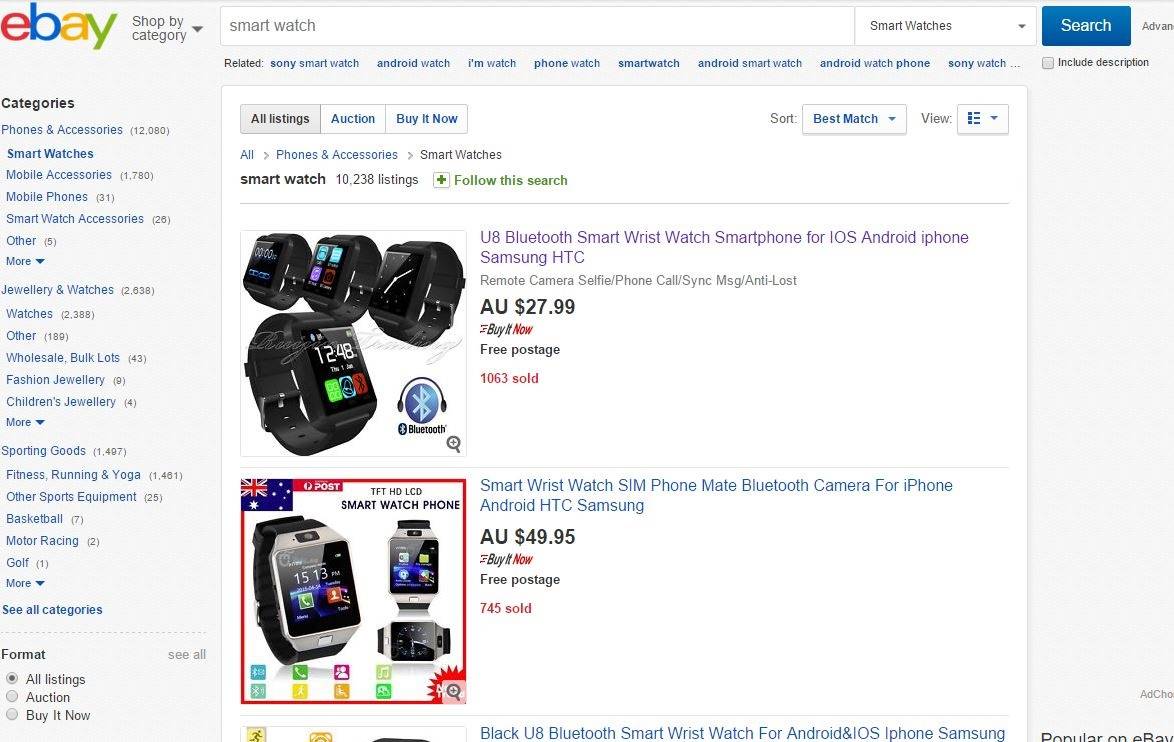
BSides SF A cheap smart watch often peddled on eBay uses a pairing app for Android or iOS that contains a backdoor that quietly connects to an unknown Chinese IP address.
The U8 watch sells for just US$17 and offers a 1.48" touch screen, Bluetooth to connect to either Android or IoS phones and the ability to make or answer calls. The Android companion app for the device can access contacts, call and SMS histories.
Mobile Iron research director Michael Raggo (@datahiding) told the BSides San Francisco conference the watch is a threat to individual and enterprise security.
"We ran dynamic and behavioural analysis (on the pairing app) and discovered that when it was paired, it started communicating outbound over a random IP address to China," Raggo said.
"We don't know what the IP address is. "In terms of corporate espionage, in terms of risk, there's definitely a lot of suspicious behaviours there."
Raggo said buyers download the pairing app from an IP address scrawled on a piece of paper that comes with the u8 watch.
The U8 and its Nucleus operating system is one of multiple watches Raggo and his team studied including the Samsung Gear 2 running Samsung Tizen, the Apple Watch running WatchOS, and the Moto 360 sporting Android Wear.
"If you are worried about fragmentation of Android, just take a look at smart watches," he said.
Raggo published the SWATtack tool which he says is useful for forensics and attacking watches. The Python tool can identify vulnerabilities in smart watches and pairing apps.
It can also bypass PIN protection and siphon data from Samsung Gear 2 Neo watches using a since disclosed and patched vulnerability. ®