This article is more than 1 year old
Magnitude malvertisers spew 400 attacks from abused Scot ad firm
Can't fault their work ethic.
Malwarebytes researcher Jerome Segura says more than 400 malicious advertisements have been shipped through ad network AdsTerra in two weeks.
The advertisements are slinging the hugely successful Magnitude exploit kit which has been the most impactful and prolific of exploit kits used in recent malvertising campaigns.
Emails to Scotland-headquartered AddTerra bounced and it could not be reached through any listed address by the time of publication.
Segura says he has seen more than 400 malvertising attacks utilising AdsTerra in recent weeks.
"In the past two weeks, we have documented over 400 unique malvertising incidents coming out of AdsTerra," Segura says.
"These malicious advertisements were displayed on a variety of adult sites and torrent portals and the ultimate payload was the Cerber ransomware.
"The Magnitude exploit kit has been on the forefront of most of the malvertising-driven attacks we have seen in the past few weeks."
| feature: Malware menaces poison ads as Google, Yahoo! look away. |
Segura says the Magnitude malvertising wave has overshadowed other attack types including those perpetrated with the Angler exploit kit, or malware distribution through hacked websites. He says victims that are not compromised are shipped off to tech support scams where criminals will attempt to convince users they have malware installed on their machines and that they must pay for some antivirus program.
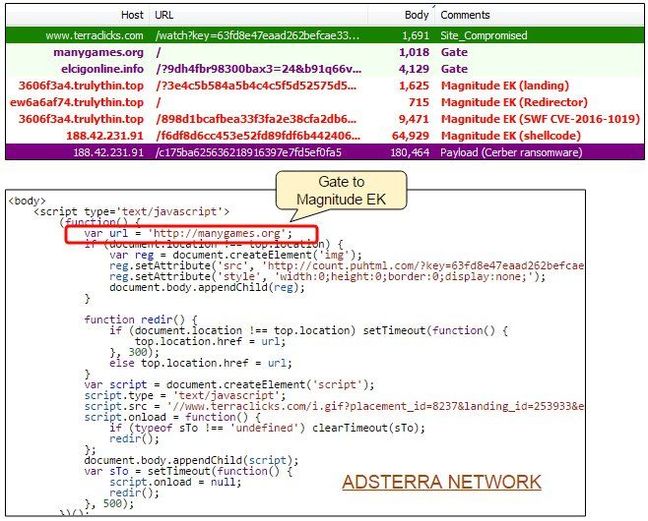
Magnitude has had a clever update of late meaning victim machines can be fingerprinted before exploit kits are delivered, a feat that helps increase the infection success rate and noise from failed compromise attempts. The exploit kit has also sported an Adobe Flash Player zero-day which coders thankfully botched. ®
